Agentic AI: The Next Frontier for Enterprises

Agentic AI represents a significant leap forward. "These systems can perform
complex reasoning, integrate with vast enterprise datasets and execute
processes autonomously. For instance, a task like merging customer accounts,
which traditionally required ticket creation and days of manual effort, can
now be completed in seconds with agentic AI," said Arun Kumar Parameswaran ...
Salesforce's Agentforce, unveiled at Dreamforce 2024, represents a significant
milestone. Built on the company's Atlas reasoning engine and using models such
as OpenAI's GPT-4 and Google's Gemini, Agentforce combines advanced AI with
Salesforce's extensive ecosystem of customer engagement data. Agentforce marks
the "third wave of AI," said Marc Benioff, CEO of Salesforce. He predicts a
massive 1 billion AI agents by 2026. Unlike earlier waves, which focused on
predictive analytics and conversational bots, this phase emphasizes
intelligent agents capable of autonomous decision-making. Salesforce has
amassed years of customer engagement data, workflows and metadata, making
Agentforce a precision tool that understands and anticipates customer
needs.
Get started with bootable containers and image mode for RHEL

Bootable containers, also provided as image mode for Red Hat Enterprise Linux,
represent an innovation in merging containerization technology with full
operating system deployment. At their core, bootable containers are OCI (Open
Container Initiative) container images that contain a complete Linux system,
including the kernel and hardware support. This approach has several
characteristics, namely:Immutability: The entire system is treated as an
immutable unit, reducing configuration drift and enhancing security (other
than /etc and /var, all directories are mounted read-only once deployed on a
physical or virtual machine). Atomic updates: System updates can be performed
as atomic operations, simplifying rollbacks and ensuring system consistency.
Standardized tooling: Leverages existing OCI container tools and workflows,
reducing the learning curve for teams familiar with containerization, and the
ability to design a complete OS environment using a Containerfile as a
blueprint. This is a wonderful benefit for a variety of use cases, including
edge computing and IoT devices (where consistent, easily updatable system
images are crucial), as well as on general cloud-native infrastructure to
enable infrastructure-as-code practices at the OS level.
Traditional EDR won't cut it: why you need zero trust endpoint security

The development of EDR tools was the next step in cyber resiliency after
antivirus began falling behind in its ability to stop malware. The struggle
began when the rate at which new malware was created and distributed far
outweighed the rate at which they could be logged and prevented from causing
harm. The most logical step to take was to develop a cybersecurity tool that
could identify malware by actions taken, not just by code. ... cybercriminals
are now using AI to streamline their malware generation process, creating
malware at faster speeds and improving its ability to run without detection.
Another crucial problem with traditional EDRs and other detection-based tools
is that they do not act until the malware is already running in the
environment, which leads them to fail customers and miss cyberattacks until it
is already too late. ... With application allowlisting, you create a list of
the applications and software you trust and need and block everything else
from running. Allowlisting is a zero trust method of application control that
prevents known and unknown threats from running on your devices, preventing
cyberattacks, like ransomware, from detonating.
AI and the future of finance: How AI is empowering NBFCs
AI in Non-Banking Financial Companies can be used for one of the first
applications – the evaluation of credit risk. Until now, lenders relied mainly
on credit scoring models and legacy data on a client. However, such models
often do not grasp the complexity of a person’s business’s financial profile,
a common problem in countries with large informal economies. AI, on the other
hand, can analyse large amounts of data, from historical transaction
information to phone use and even social behaviour. AI algorithms are able to
analyse this data at astonishing speed, recognising trends and yielding more
precise forecasts about the borrower’s capability to pay back loans. This
enables NBFCs to offer credit to a wider and more diverse client base, which
ultimately drives financial inclusion. ... The function of AI extends beyond
just providing transactional support. With the help of sophisticated
machine-learning models, NBFCs are able to offer personalised financial
products that are tailored to the financial behaviour of individual
preferences, lifestyles, and conditions. ... By using advanced analytics and
machine-learning models, NBFCs are able to identify new opportunities to
grow.
Achieving Success in the New Era of AI-Driven Data Management

AI-driven personalization is essential for companies looking to stand out in a
competitive marketplace. By leveraging vast amounts of customer data, AI helps
businesses create highly tailored experiences that adapt to individual user
preferences, increasing engagement and loyalty. Recent research shows "that 81
percent of customers prefer companies that offer a personalized experience."
... AI-driven data analytics has significant ethical, privacy, and regulatory
challenges. Ethical considerations, such as bias detection and mitigation, are
necessary to ensure AI models provide fair and accurate outcomes. Implementing
governance frameworks and transparency in AI decision-making builds trust by
making algorithms' logic accessible and accountable, minimizing the risk of
unintended discrimination in data-driven insights. Data privacy and security
are equally critical. The increased use of techniques like differential
privacy raises expectations of high privacy standards. Differential privacy
adds carefully calibrated "noise" to data sets — random variations designed to
prevent the re-identification of individuals while still allowing accurate
aggregate insights.
Riding the wave of digital transformation: Insights and lessons from Japan’s journey

Availability and accessibility of digital infrastructure is often inadequate
in developing countries, preventing digital services from reaching everyone.
Japan’s experience in this domain ranges from formulating national strategies
for digital infrastructure development to providing affordable high-speed
internet access, and to integrating and standardizing different systems. The
key takeaway here is the importance of sustaining robust infrastructure
investment over a period of time and providing room for digital system
scalability and flexibility. ... With this in mind, Japan embraced innovative
approaches to enhance people’s digital skills. Some cities like Kitakyushu are
training staff to use minimal coding tools—software that allows them to design
applications with simple codes— as well as providing other training on digital
transformation to equip staff at various levels within local governments with
relevant skills. ... Digital transformation relies on coordinated efforts: the
Japanese central government established supportive policies and frameworks,
while local governments translated these into actionable initiatives for
public benefit.
When Hackers Meet Tractors: Surprising Roles in IoT Security

IoT encompasses the billions of connected devices we use daily - everything
from smart home gadgets to fitness trackers. IIoT focuses on industrial
applications, such as manufacturing robots, energy grid systems and autonomous
vehicles. While these technologies bring remarkable efficiencies, they also
expand the potential attack surface for cybercriminals. Ransomware, data
breaches, and system takeovers are no longer just concerns for tech companies
- they’re threats to every industry that relies on connectivity. ... Breaking
into IoT and IIoT cybersecurity may seem daunting, but the pathway is more
accessible than you might think. Leverage transferable skills. Many
professionals transition into IoT/IIoT roles by building on their existing
cybersecurity expertise. For instance, knowledge of network security or
ethical hacking can be adapted to these environments. It is also beneficial to
pursue specialized certifications that can demonstrate your expertise and open
doors in niche fields. ... GICSP is designed specifically for professionals
working in industrial environments, such as manufacturing, energy, or
transportation. It bridges the gap between IT, OT (Operational Technology),
and IIoT, emphasizing the secure operation of industrial control systems.
How to Ensure Business Continuity for Banks and Financial Services

A business continuity plan is only as effective as the people behind it.
Creating a culture of safety and preparedness throughout a financial services
organization is key to a successful crisis response. Regular training
sessions, disaster simulations, and frequent updates to the BCP keep teams
ready and capable of responding efficiently. Facilities teams must have a
clear understanding of their roles and responsibilities during a disruption.
From decision-makers to on-the-ground personnel, each team member should know
exactly what steps to take to restore operations. Clear protocols ensure that
recovery efforts can be executed quickly, minimizing service interruptions and
maintaining a seamless customer experience. Disasters may be inevitable, but
with the right facilities management strategies in place, financial service
companies can be well-prepared to respond effectively and ensure business
continuity. From conducting risk assessments to leveraging technology and
building strong vendor partnerships, proactive facilities management can be
the difference between a rapid recovery and prolonged downtime. Now is the
time to assess the current state of facilities, ensure teams are trained, and
confirm that business continuity plans are robust.
Enterprises Ill-prepared to Realize AI’s Potential

To build more AI infrastructure readiness, skilled talent will be key to
overcoming a deficit in workers needed to maintain IT infrastructure,
Patterson suggests. In fact, only 31% of companies believed their talent was
in a “high state of readiness” to fully make use of AI. In addition, 24% of
those surveyed did not believe their companies held enough talent to address
the “growing demand for AI,” the Cisco report revealed. Expanding the AI
talent pool will require forming a learning culture for innovation, he says.
That includes talent development and forming clear career paths. Leadership
feels the pressure to achieve AI readiness, but workers are hesitant to use
AI, according to the Cisco AI readiness report. “While organizations face
pressure from leadership to bring in AI, the disconnect is likely due to
hesitancy among workers within the organization who must take steps to gain
new skills for AI or fear AI taking over their jobs,” Patterson says. ... “If
you can’t secure AI, you won’t be able to successfully deploy AI,” he says.
Meanwhile, tech professionals should develop a holistic view of the
infrastructure required to adopt AI while incorporating observability and
security, according to Patterson. A holistic view of infrastructure will bring
“easier operations, resiliency, and efficiency at scale,” Patterson says.
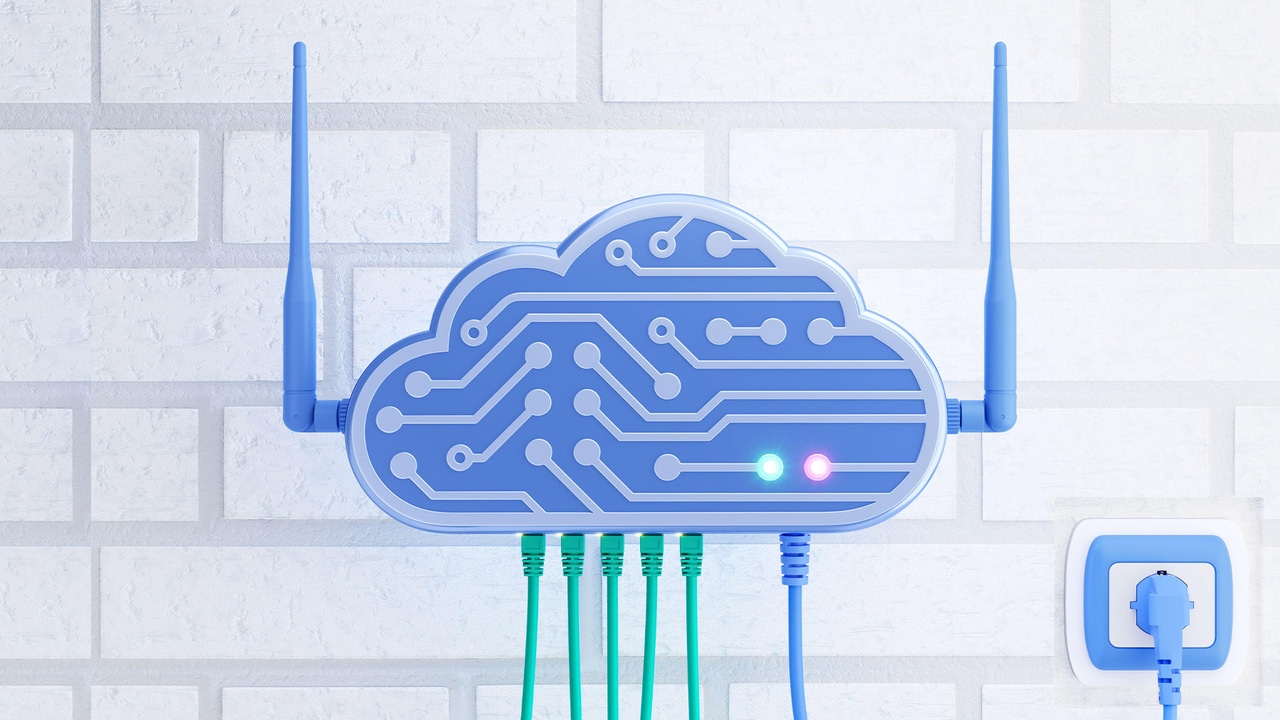
The Role of Edge-to-Cloud Infrastructure in Shaping Digital Transformation

Unlike the cloud transporting data to the cloud for processing, Edge
infrastructure brings the distributed computing network closer to the
users–and is powered by local, small computing power near the end- user and
relies on the cloud only as a ‘director’ of operations. This Edge-to-cloud
computing model allows IoT devices to stay small and affordable. It
also allows localized computing power to expedite data processing across many
applications without relying on high throughput and consistent connectivity to
a cloud hyper-scale or other data center hundreds or thousands of miles
away. ... The key to edge computing is handling sizeable amounts of data that
IoT devices can produce in conjunction with the existing inbuilding systems
that would be difficult, risky, or cost-prohibitive to supplant. Given IoT
devices and existing systems often provide raw and isolated data – IoT
platforms consolidate, aggregate, and then analyze data in real-time, or farm
it out to external tools in the cloud for specific needs (work order
management, MOPs, etc.). The key here is not just about real-time context,
given that IoT platforms provide a database of historical information – true
actionable outcomes can be driven from data.
Quote for the day:
"Before you are a leader, success is
all about growing yourself. When you become a leader, success is all about
growing others" -- Jack Welch























/dq/media/media_files/2024/11/22/ECd4uE6hGEeyELEJRH39.jpg)






