Can Open Source Sustain Itself without Losing Its Soul?

It’s clear that businesses will need to play more of a role in open source. As
Valsorda noted in the same blog post, “open source sustainability and supply
chain security are on everyone’s slide decks, blogs, and press releases. Big
companies desperately need the open source ecosystem to
professionalize.” Amanda Brock, CEO of OpenUK, a not-for-profit that
supports the use of open technologies, concurred: “We need to know not only that
we have the best software that can be produced — which collaborative and diverse
globally produced open source software is — but also that appropriate funding
has been provided to ensure that those building all this essential software are
able to maintain and support it being secure.” Brock cited a number of examples
of where this is happening in the U.K.; for example, she pointed to the work of
the Energy Digitalisation Taskforce. That governmental group “suggested that the
spine of the digitalized energy sector should be built on open source software.
The National Health Service in the U.K. also now has an open source
software-first approach for code it creates that it is increasingly trying to
live by.”
Using the Business Model Canvas in Enterprise Architecture

The Business Model Canvas brings together nine key elements of a business model,
making it possible to observe and describe the relationships of those nine
elements to each other. As architects, plotting the relationship of one element
to other elements is familiar territory. We align patterns, find gaps, map gives
and gets, and understand strategy by assessing the relationships of the critical
systems in an architecture landscape. The Business Model Canvas is yet another
tool to help us convey understanding. Many enterprise architects hang their hats
on “People, Process, Technology,” the popular PPT framework popularized in the
1990s. The roots of PPT extend further back, to the 1960s and the Diamond Model
from Harold Leavitt. PPT and the Diamond Model are useful, for certain, but the
canvas offers something that every enterprise architect should value. In the
aggregate, the nine blocks tell the story of the organization, how it goes to
market and aims to create, deliver, and capture value...”
How Enterprise Architecture Helps Reduce IT Costs

Easier said than done with the traditional process of manual follow-ups hampered
by inconsistent documentation often scattered across many teams. The issue with
documentation also often means that maintenance efforts are duplicated,
resources that could have been better deployed elsewhere. The result is the
equivalent of around 3 hours of a dedicated employee’s focus per application per
year spent on documentation, governance, and maintenance. Not so for the
organization that has a digital-native EA platform that leverages your data to
enable scalability and automation in workflows and messaging so you can reach
out to the most relevant people in your organization when it's most needed.
Features like these can save an immense amount of time otherwise spent
identifying the right people to talk to and when to reach out to them, making
your enterprise architecture the single source of truth and a solid foundation
for effective governance. The result is a reduction of approximately a third of
the time usually needed to achieve this.
AI drug algorithms can be flipped to invent bioweapons
Now consider an AI algorithm that can generate deadly biochemicals that behave
like VX but are made up of entirely non-regulated compounds. "We didn't do this
but it is quite possible for someone to take one of these models and use it as
an input to the generative model, and now say 'I want something that is toxic',
'I want something that does not use the current precursors on the watch list'.
And it generates something that's in that range. We didn't want to go that extra
step. But there's no logical reason why you couldn't do that," Urbina added. If
it's not possible to achieve this, you're back to square one. As veteran drug
chemist Derek Lowe put it: "I'm not all that worried about new nerve agents ...
I'm not sure that anyone needs to deploy a new compound in order to wreak havoc
– they can save themselves a lot of trouble by just making Sarin or VX, God help
us." There is no strict regulation on the machine-learning-powered synthesis of
new chemical molecules.
A Primer on Proxies

In HTTP/2, each request and response is sent on a different stream. To support
this, HTTP/2 defines frames that contain the stream identifier that they are
associated with. Requests and responses are composed of HEADERS and DATA frames
which contain HTTP header fields and HTTP content, respectively. Frames can be
large. When they are sent on the wire they might span multiple TLS records or
TCP segments. Side note: the HTTP WG has been working on a new revision of the
document that defines HTTP semantics that are common to all HTTP versions. The
terms message, header fields, and content all come from this description. HTTP/2
concurrency allows applications to read and write multiple objects at different
rates, which can improve HTTP application performance, such as web browsing.
HTTP/1.1 traditionally dealt with this concurrency by opening multiple TCP
connections in parallel and striping requests across these connections. In
contrast, HTTP/2 multiplexes frames belonging to different streams onto the
single byte stream provided by one TCP connection.
Thinking Strategically Will Help You Get Ahead and Stay Ahead
Create mental space for new ideas to kick-in. Without the quiet time to sit with
your thoughts, facing the uncomfortable silence, and letting your mind wander
away, you cannot draw useful connections. It will not happen the first time
around and probably not even the second time. But if you are persistent in your
efforts, without digital and other distractions of daily life, you will start to
notice new patterns of thinking. New ideas that you never thought about before
will start to surface. Another great strategy is to not restrict yourself to
knowledge within your current scope of work. Spend time learning about your
business and industry. Meet with other functions within your organization to
understand how they operate, what their challenges are and how they make
decisions. All of this knowledge will enable you to apply different mental
models to connect ideas from different domains thereby expanding your circle of
competence and building your strategic thinking skills. Remember, building
strategic thinking skills involves looking beyond the obvious and now to
prodding and shaping the uncertain future.
Microsoft Azure reveals a key breakthrough toward scaling quantum computing

“It’s never been done before, and until now it was never certain that it could
be done. And now it’s like yes, here’s this ultimate validation that we’re on
the right path,” she said. What have researchers achieved? They have developed
devices capable of inducing a topological phase of matter bookended by a pair of
Majorana zero modes, types of quantum excitations first theorized about in 1937
that don’t normally exist in nature. Majorana zero modes are crucial to
protecting quantum information, enabling reliable computation, and producing a
unique type of qubit, called a topological qubit, which Microsoft’s quantum
machine will use to store and compute information. A quantum computer built with
these qubits will likely be more stable than machines built with other types of
known qubits and may help solve some of the problems which currently baffle
classical computers. “Figuring out how to feed the world or cure it of climate
change will require discoveries or optimization of molecules that simply can’t
be done by today’s classical computers
Lensless Camera Captures Cellular-Level 3D Details
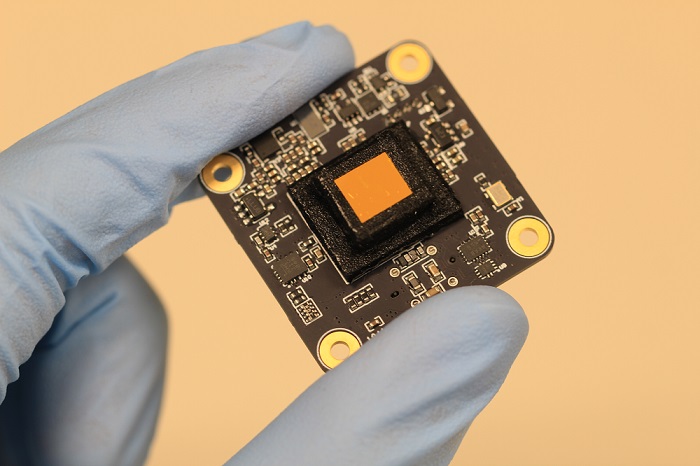
At the sensor, light that comes through the mask appears as a point spread
function, a pair of blurry blobs that seems useless but is actually key to
acquiring details about objects below the diffraction limit that are too small
for many microscopes to see. The blobs’ sizes, shapes, and distances from each
other indicate how far the subject is from the focal plane. Software
reinterprets the data into an image that can be refocused at will. The
researchers first tested the device by capturing cellular structures in a lily
of the valley, and then calcium activity in small jellyfish-like hydra. The team
then monitored a running rodent, attaching the device to the rodent’s skull and
then setting the animal down on a wheel. Data showed fluorescent-tagged neurons
in a region of the animal’s brain, connecting activity in the motor cortex with
motion and resolving blood vessels as small as 10 µm in diameter. In
collaboration with Rebecca Richards-Kortum and research scientist Jennifer Carns
from Rice Bioengineering, the team identified vascular imaging as a potential
clinical application of the Bio-FlatScope.
Handling Out-of-Order Data in Real-Time Analytics Applications

The solution is simple and elegant: a mutable cloud native real-time analytics
database. Late-arriving events are simply written to the portions of the
database they would have been if they had arrived on time in the first place. In
the case of Rockset, a real-time analytics database that I helped create,
individual fields in a data record can be natively updated, overwritten or
deleted. There is no need for expensive and slow copy-on-writes, a la Apache
Druid, or kludgy segregated dynamic partitions. A mutable real-time analytics
database provides high raw data ingestion speeds, the native ability to update
and backfill records with out-of-order data, all without creating additional
cost, data error risk or work for developers and data engineers. This supports
the mission-critical real-time analytics required by today’s data-driven
disruptors. In future blog posts, I’ll describe other must-have features of
real-time analytics databases such as bursty data traffic and complex queries.
CISOs face 'perfect storm' of ransomware and state-supported cybercrime
With not just ransomware gangs raiding network after network, but nation states
consciously turning a blind eye to it, today's chief information security
officers are caught in a "perfect storm," says Cybereason CSO Sam Curry.
"There's this marriage right now of financially motivated cybercrime that can
have a critical infrastructure and economic impact," Curry said during a CISO
roundtable hosted by his endpoint security shop. "And there are some nation
states that do what we call state-ignored sanctioning," he continued, using
Russia-based REvil and Conti ransomware groups as examples of criminal
operations that benefit from their home governments looking the other way. "You
get the umbrella of sovereignty, and you get the free license to be a privateer
in essence," Curry said. "It's not just an economic threat. It's not just a
geopolitical threat. It's a perfect storm." It's probably not a huge surprise to
anyone that destructive cyberattacks keep CISOs awake at night.
Quote for the day:
"Leadership means forming a team and
working toward common objectives that are tied to time, metrics, and
resources." -- Russel Honore