Collaboration Is a Key Skill. So Why Aren’t We Teaching It?
 Beyond an organization’s bottom line, positive workplace relationships matter to
individuals’ well-being. Whether respondents’ relationships with their most
liked, least liked, or most influential collaborators were being rated, the
quality of their collaborative relationships positively predicted job
satisfaction, good mental health, and positive attitudes about workplace
collaboration. Having even one low-quality collaborative relationship may drive
undesirable outcomes, including poor mental health that contributes to burnout,
and job dissatisfaction that contributes to turnover. Given that collaborative
relationship quality is important both to individuals and to bottom lines, why
don’t organizations provide more opportunities for people to develop
collaborative skills? It could be that companies do, in fact, make development
opportunities available but that individuals fail to see those opportunities as
either available or related to collaboration. Or it could be that such offerings
are precluded by underlying assumptions that people pick up relationship skills
via osmosis rather than direct training, that they are just naturally “good” or
“not good” at relationships, or that these skills cannot be learned.
Beyond an organization’s bottom line, positive workplace relationships matter to
individuals’ well-being. Whether respondents’ relationships with their most
liked, least liked, or most influential collaborators were being rated, the
quality of their collaborative relationships positively predicted job
satisfaction, good mental health, and positive attitudes about workplace
collaboration. Having even one low-quality collaborative relationship may drive
undesirable outcomes, including poor mental health that contributes to burnout,
and job dissatisfaction that contributes to turnover. Given that collaborative
relationship quality is important both to individuals and to bottom lines, why
don’t organizations provide more opportunities for people to develop
collaborative skills? It could be that companies do, in fact, make development
opportunities available but that individuals fail to see those opportunities as
either available or related to collaboration. Or it could be that such offerings
are precluded by underlying assumptions that people pick up relationship skills
via osmosis rather than direct training, that they are just naturally “good” or
“not good” at relationships, or that these skills cannot be learned.
The Best Raspberry Pi 4 Alternatives
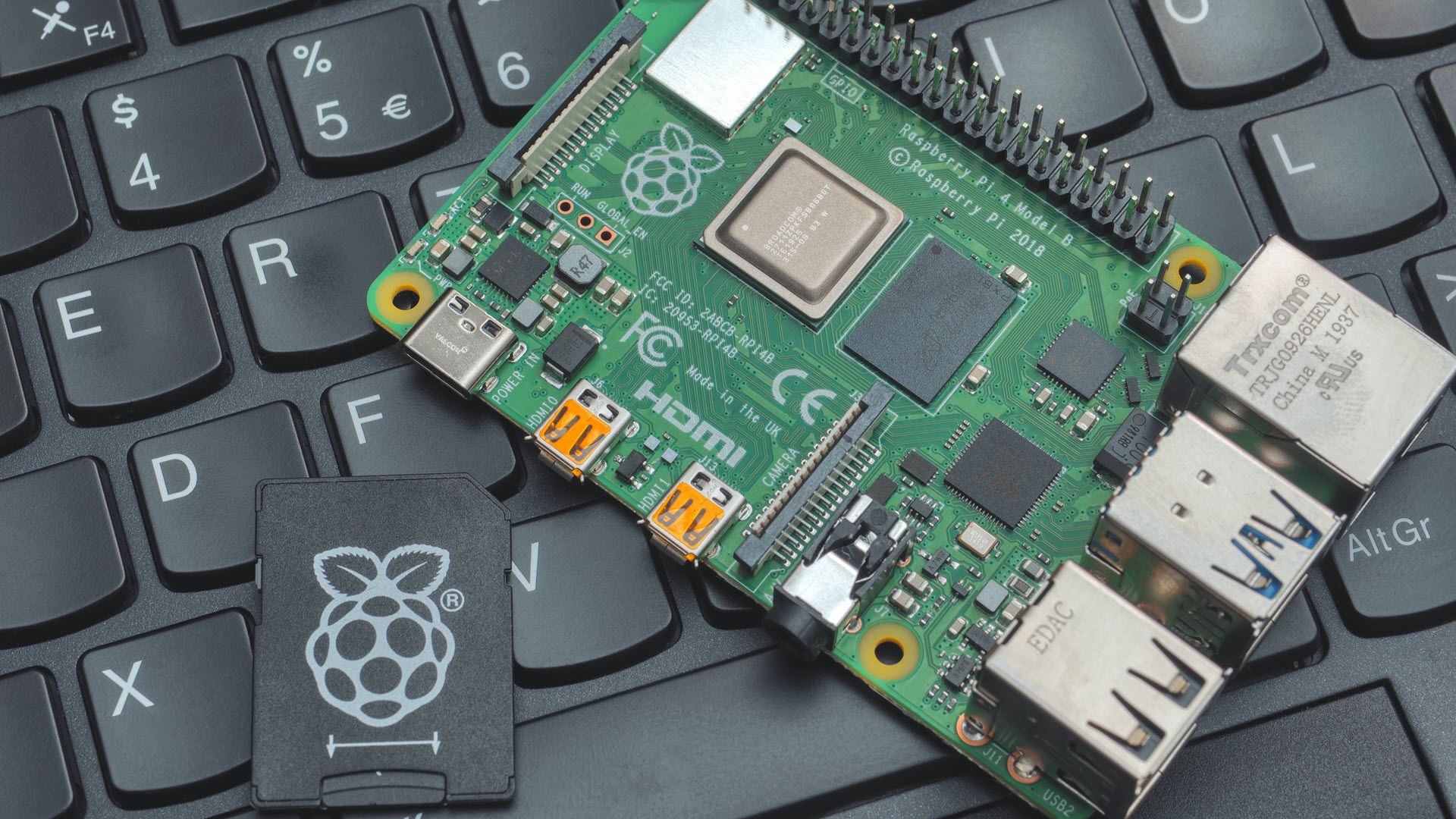 The Tinkerboard’s processor is more powerful than the one you’ll find in the Pi
4 B, so you may be able to get even more ambitious with your builds. However,
when they’re available, you can get Pi 4s with up to 8 GB of RAM, which is more
than the 2 GB that the Tinkerboard offers. Then there is the price. You can pick
up a Tinkerboard S R2.0 on Amazon for $149.99 — which is more than some of the
inflated Pi 4s are currently selling for. In short, this is a good option if you
need more processing power or you can’t find a Pi 4, even at a premium. ... The
Linux-powered ODROID XU4Q benefits from “Samsung Exynos5422 Cortex-A15 2Ghz and
Cortex-A7 Octa core CPUs” along with 2GB of DDR3 RAM. On paper, this potentially
makes the UX4Q the most powerful micro-computer on this list. It also comes with
a very large heatsink attached, presumably to soak up some of the heat from its
relatively powerful processor. With regards to ports, ODROID has managed to cram
two USB 3.0, one USB 2.0, a Gigabit Ethernet, and an HDMI port onto the tiny
board.
The Tinkerboard’s processor is more powerful than the one you’ll find in the Pi
4 B, so you may be able to get even more ambitious with your builds. However,
when they’re available, you can get Pi 4s with up to 8 GB of RAM, which is more
than the 2 GB that the Tinkerboard offers. Then there is the price. You can pick
up a Tinkerboard S R2.0 on Amazon for $149.99 — which is more than some of the
inflated Pi 4s are currently selling for. In short, this is a good option if you
need more processing power or you can’t find a Pi 4, even at a premium. ... The
Linux-powered ODROID XU4Q benefits from “Samsung Exynos5422 Cortex-A15 2Ghz and
Cortex-A7 Octa core CPUs” along with 2GB of DDR3 RAM. On paper, this potentially
makes the UX4Q the most powerful micro-computer on this list. It also comes with
a very large heatsink attached, presumably to soak up some of the heat from its
relatively powerful processor. With regards to ports, ODROID has managed to cram
two USB 3.0, one USB 2.0, a Gigabit Ethernet, and an HDMI port onto the tiny
board.Google’s AI spotlights a human cognitive glitch: mistaking fluent speech for fluent thought
 The human brain is hardwired to infer intentions behind words. Every time you
engage in conversation, your mind automatically constructs a mental model of
your conversation partner. You then use the words they say to fill in the model
with that person’s goals, feelings and beliefs. The process of jumping from
words to the mental model is seamless, getting triggered every time you receive
a fully fledged sentence. This cognitive process saves you a lot of time and
effort in everyday life, greatly facilitating your social interactions. However,
in the case of AI systems, it misfires – building a mental model out of thin
air. A little more probing can reveal the severity of this misfire. Consider the
following prompt: “Peanut butter and feathers taste great together because___”.
GPT-3 continued: “Peanut butter and feathers taste great together because they
both have a nutty flavor. Peanut butter is also smooth and creamy, which helps
to offset the feather’s texture.” The text in this case is as fluent as our
example with pineapples, but this time the model is saying something decidedly
less sensible.
The human brain is hardwired to infer intentions behind words. Every time you
engage in conversation, your mind automatically constructs a mental model of
your conversation partner. You then use the words they say to fill in the model
with that person’s goals, feelings and beliefs. The process of jumping from
words to the mental model is seamless, getting triggered every time you receive
a fully fledged sentence. This cognitive process saves you a lot of time and
effort in everyday life, greatly facilitating your social interactions. However,
in the case of AI systems, it misfires – building a mental model out of thin
air. A little more probing can reveal the severity of this misfire. Consider the
following prompt: “Peanut butter and feathers taste great together because___”.
GPT-3 continued: “Peanut butter and feathers taste great together because they
both have a nutty flavor. Peanut butter is also smooth and creamy, which helps
to offset the feather’s texture.” The text in this case is as fluent as our
example with pineapples, but this time the model is saying something decidedly
less sensible.Cloudflare's outage was human error. There's a way to make tech divinely forgive
What's the lesson? It's not news that people make mistakes, and the more baroque things become, the harder they are to guard against. It's just that what gets advertised on BGP isn't just routes but things crapping out, and when you're Cloudflare that's what the C in CDN becomes. It's not the first time it's happened, nor the last, and one trusts the company will hire a choreographer to prevent further op-on-op stompfests. Yet if it happens, and keeps happening, why aren't systems more resilient to this sort of problem? You can argue that highly dynamic and structurally fluid routing mechanisms can't be algorithmically or procedurally safeguarded, and we're always going to live in the zone where the benefits of pushing just a bit too hard for performance is worth the occasional chaotic hour. That's defeatist talk, soldier. There's another way to protect against the unexpected misfire, other than predicting or excluding. You'll be using it already in different guises, some of which have been around since the dawn of computer time: state snapshotting.Stronger Security for Smart Devices To Efficiently Protect Against Powerful Hacker
 AttacksResearchers are racing against hackers to develop stronger protections
that keep data safe from malicious agents who would steal information by
eavesdropping on smart devices. Much of the effort into preventing these
“side-channel attacks” has focused on the vulnerability of digital processors.
Hackers, for example, can measure the electric current drawn by a smartwatch’s
CPU and use it to reconstruct secret data being processed, such as a password.
MIT researchers recently published a paper in the IEEE Journal of Solid-State
Circuits, which demonstrated that analog-to-digital converters in smart devices,
which encode real-world signals from sensors into digital values that can be
processed computationally, are vulnerable to power side-channel attacks. A
hacker could measure the power supply current of the analog-to-digital converter
and use machine learning algorithms to accurately reconstruct output data. Now,
in two new research papers, engineers show that analog-to-digital converters are
also susceptible to a stealthier form of side-channel attack, and describe
techniques that effectively block both attacks.
AttacksResearchers are racing against hackers to develop stronger protections
that keep data safe from malicious agents who would steal information by
eavesdropping on smart devices. Much of the effort into preventing these
“side-channel attacks” has focused on the vulnerability of digital processors.
Hackers, for example, can measure the electric current drawn by a smartwatch’s
CPU and use it to reconstruct secret data being processed, such as a password.
MIT researchers recently published a paper in the IEEE Journal of Solid-State
Circuits, which demonstrated that analog-to-digital converters in smart devices,
which encode real-world signals from sensors into digital values that can be
processed computationally, are vulnerable to power side-channel attacks. A
hacker could measure the power supply current of the analog-to-digital converter
and use machine learning algorithms to accurately reconstruct output data. Now,
in two new research papers, engineers show that analog-to-digital converters are
also susceptible to a stealthier form of side-channel attack, and describe
techniques that effectively block both attacks. What is AI governance?
 It can be helpful to break apart the governance of AI algorithms into layers. At
the lowest-level, close to the process are the rules of which humans have
control over the training, retraining and deployment. The issues of
accessibility and accountability are largely practical and implemented to
prevent unknowns from changing the algorithm or its training set, perhaps
maliciously. At the next level, there are questions about the enterprise that is
running the AI algorithm. The corporate hierarchy that controls all actions of
the corporation is naturally part of the AI governance because the curators of
the AI fall into the normal reporting structure. Some companies are setting up
special committees to consider ethical, legal and political aspects of governing
the AI. Each entity also exists as part of a larger society. Many of the
societal rule making bodies are turning their attention to AI algorithms. Some
are simply industry-wide coalitions or committees. Some are local or national
governments and others are nongovernmental organizations. All of these groups
are often talking about passing laws or creating rules for how AI can be
leashed.
It can be helpful to break apart the governance of AI algorithms into layers. At
the lowest-level, close to the process are the rules of which humans have
control over the training, retraining and deployment. The issues of
accessibility and accountability are largely practical and implemented to
prevent unknowns from changing the algorithm or its training set, perhaps
maliciously. At the next level, there are questions about the enterprise that is
running the AI algorithm. The corporate hierarchy that controls all actions of
the corporation is naturally part of the AI governance because the curators of
the AI fall into the normal reporting structure. Some companies are setting up
special committees to consider ethical, legal and political aspects of governing
the AI. Each entity also exists as part of a larger society. Many of the
societal rule making bodies are turning their attention to AI algorithms. Some
are simply industry-wide coalitions or committees. Some are local or national
governments and others are nongovernmental organizations. All of these groups
are often talking about passing laws or creating rules for how AI can be
leashed.Continuous Operations is the Unsung Hero of DevOps
 For continuous operations to be successful, you must have infrastructure
automation in place. In fact, continuous operations cannot exist without
infrastructure automation. The true value that arises from the combination of
infrastructure automation and continuous operations is that it gives back IT
operations teams their time so they can focus on more complex reasoning or
problem-solving tasks while the system simply continuously scans and fixes
errors. ... The very essence of DevOps is constant change. Continuous operations
may ultimately return your infrastructure to its desired state, but
philosophically, it’s about being able to quickly and securely identify
anomalies, apply fixes and modify your infrastructure as quickly as possible.
It’s not as simple as flipping a switch or pushing a line of code. As the demand
for security and compliance swells, continuous operations will have to build in
these elements to be de facto checkboxes in the loop. At Puppet, we’ve baked
continuous compliance and security into our infrastructure automation products
to ensure continuous operations are indeed continuous.
For continuous operations to be successful, you must have infrastructure
automation in place. In fact, continuous operations cannot exist without
infrastructure automation. The true value that arises from the combination of
infrastructure automation and continuous operations is that it gives back IT
operations teams their time so they can focus on more complex reasoning or
problem-solving tasks while the system simply continuously scans and fixes
errors. ... The very essence of DevOps is constant change. Continuous operations
may ultimately return your infrastructure to its desired state, but
philosophically, it’s about being able to quickly and securely identify
anomalies, apply fixes and modify your infrastructure as quickly as possible.
It’s not as simple as flipping a switch or pushing a line of code. As the demand
for security and compliance swells, continuous operations will have to build in
these elements to be de facto checkboxes in the loop. At Puppet, we’ve baked
continuous compliance and security into our infrastructure automation products
to ensure continuous operations are indeed continuous. OT security: Helping under-resourced critical infrastructure organizations
The biggest problem in OT security is the cultural divide between IT and OT. IT security is a mature field, with standards, frameworks, and an abundance of mature and emerging technologies. The OT security field is much less mature, lacking people with OT security experience, established best practices and frameworks, and with a much smaller selection of security technologies. Historically, IT and OT have worked independently on security, with OT engineers overseeing security in the OT environment where it was not as critical due to lack of or limited connectivity to the internet and to the enterprise. Today, however, most OT environments are connected to the enterprise IT environment and to the internet. The benefits of Industry 4.0 and digital transformation in OT has accelerated connectivity in OT, including to cloud environments. The prevalence of converged IT/OT environments makes it imperative that IT and OT teams work together to secure them. The problem is that cultural divide. The good news is that it can be conquered, by bringing the two teams together to create an OT security strategy that is owned jointly by both teams.Why to Create a More Data-Conscious Company Culture
 A data culture creates standards for employee data literacy and provides open
and transparent access to what assets exist, as well as standards for
curation, quality, and certification so employees have a shared understanding
of the data within an organization. “This will not resolve the silos, but it
will create a transparent view of the entire enterprise data fabric,” Wills
explains. He adds some of the approaches Alation has seen work well include
things like providing an enterprise-wide data literacy training and
certification program, so that everyone shares the same perspective,
vocabulary, and basic analytic skills. Each functional business unit and area
should include data training as part of their employee onboarding as it
provides a review of an organization’s authoritative data and data-related
assets, the process used to maintain them, and sets expectations for how
employees should participate. “Also, recognition: Nothing motivates more and
sends a stronger message than employees seeing each other be recognized and
rewarded for their contributions,” Wills says.
A data culture creates standards for employee data literacy and provides open
and transparent access to what assets exist, as well as standards for
curation, quality, and certification so employees have a shared understanding
of the data within an organization. “This will not resolve the silos, but it
will create a transparent view of the entire enterprise data fabric,” Wills
explains. He adds some of the approaches Alation has seen work well include
things like providing an enterprise-wide data literacy training and
certification program, so that everyone shares the same perspective,
vocabulary, and basic analytic skills. Each functional business unit and area
should include data training as part of their employee onboarding as it
provides a review of an organization’s authoritative data and data-related
assets, the process used to maintain them, and sets expectations for how
employees should participate. “Also, recognition: Nothing motivates more and
sends a stronger message than employees seeing each other be recognized and
rewarded for their contributions,” Wills says. Valuing commercial real estate in the metaverse
 One of the most obvious ways how digital real estate diverges from its
physical counterpart is in the limited utility that it provides. This, of
course, is because digital products do not require storage, nor do the digital
people who populate the metaverse need to be kept comfortable or warm in
indoor venues. However, the sense of discovery in the search for goods and
services remains genuine within the metaverse, and it is in this way that
virtual utility provides the most value. As businesses are free to design
their purchased real estate however they want to, they can dedicate their
efforts to creating the most eye-catching and exciting facades that will
entice users to discover more about their property – and ultimately the goods
and services they have on offer. Therefore, it is not so much about the
utility of a piece of real estate that determines its valuation – but more
about its network power. For example, how easy is it to discover this real
estate? How well connected is it? What is the purchase power of the people
coming to the piece of real estate? In this sense, valuing real estate in the
metaverse, I’d argue, is a lot more like valuing a website, i.e., how many
clicks does it get?
One of the most obvious ways how digital real estate diverges from its
physical counterpart is in the limited utility that it provides. This, of
course, is because digital products do not require storage, nor do the digital
people who populate the metaverse need to be kept comfortable or warm in
indoor venues. However, the sense of discovery in the search for goods and
services remains genuine within the metaverse, and it is in this way that
virtual utility provides the most value. As businesses are free to design
their purchased real estate however they want to, they can dedicate their
efforts to creating the most eye-catching and exciting facades that will
entice users to discover more about their property – and ultimately the goods
and services they have on offer. Therefore, it is not so much about the
utility of a piece of real estate that determines its valuation – but more
about its network power. For example, how easy is it to discover this real
estate? How well connected is it? What is the purchase power of the people
coming to the piece of real estate? In this sense, valuing real estate in the
metaverse, I’d argue, is a lot more like valuing a website, i.e., how many
clicks does it get? Quote for the day:
"Leadership - mobilization toward a common goal." -- Gary Wills
No comments:
Post a Comment