The CIO's guide to understanding the metaverse

The metaverse can be a fully digital realm in which people interact as avatars,
said Marty Resnick, vice president and analyst on Gartner's technology
innovation team. It can also be a mix of real-world and virtual experiences,
such as individuals in their home attending a real-world rock concert where
they're able to see, hear and interact with those attending in person. In either
case, the metaverse includes the ability to transact so that participants can
use nonfungible tokens (NFTs), cryptocurrency or some other blockchain-enabled
digital currency to buy and sell products and services and offer customer
experience (CX) through 3D reconstructions. Right now, a number of companies are
piloting initial versions of what the metaverse will be, Resnick said. But the
fully realized metaverse will rest on major advances to three areas: ability to
easily transport and conduct life in another realm, a realized 3D representation
of the physical world and a Web3 economy. "We're already seeing these three
pieces come up today, and when they all come together, that's where we'll see
the true metaverse," Resnick said.
The 3 Phases of Leadership

In my 20-plus years of experience in startups -- having filled every position
from new hire to CEO -- I've never seen a company reach its potential under
anything less than exemplary leadership. The reverse can be true, of course. Any
business can fail regardless of how good the leadership might be. But if your
company leadership sucks, your business doesn't stand a chance.
Leadership -- despite the millions of dollars and hours spent coaching
it -- isn't that difficult to wrap your brain around. You know it when you see
it, and you feel it when you lack it. In fact, the last person to realize when
leadership is starting to deteriorate is usually the leader themselves.
Self-understanding can be pretty opaque at the top. But let me save you a few
hours in a hotel ballroom listening to a bunch of people who used to lead things
you've kind of heard of. With almost any company, team, or project -- leadership
has three distinct phases over time. The trick is getting to the right one and
staying there as long as you can. The good news is that once you come to terms
with which leadership phase you're in, it isn't terribly difficult to right your
own ship.
Neural networks, the machine learning algorithm based on the human brain
If you programmed a computer to do something, the computer would always do the
same thing. It would react to certain situations the way you “told” it to. This
is what an algorithm is: a set of instructions to solve a certain kind of
problem. But there are limitations in the instructions that humans can write
down in a code. We can’t use a simple code to teach a computer how to interpret
the natural language or how to make predictions, in effect how to "think" for
itself. This is because a code can't be large enough to cover all possible
situations, such as all of the decisions we make when we drive - like predicting
what other drivers will do and deciding what we will do based on that. However,
a computer is not able to react differently or correctly to these special
conditions because it simply does not (or cannot) have pre-configured specific
responses to them. But what if it could figure them out by itself? This is what
machine learning is for —to “train” computers to learn from data and develop
predictive capacities and decision-making abilities.
What Generation Z can teach us about cybersecurity
As we discussed the impact of a growing reliance on technology to share
information among friends and family, attend school during the pandemic, run
businesses, and more, the group considered what exactly should society seek to
prevent, protect, preserve, and advance with technology. “The government and
industry should do more to prepare digital citizens for breaches or attacks that
may compromise personal data and privacy,” according to Sama, an 18-year-old
pursuing an interest in geopolitics and counterterrorism. She began using social
media in elementary school and signed various consent forms regarding the use of
her data. While aggregation of user data is not all bad—information can feed
technology innovation—there need to be enhanced protections for youth on social
media platforms, particularly around consent. “Women and girls are empowered and
more secure when they can claim more agency in their lives, especially in
settings when they are not given choices,” explained Jasmine, a 19-year-old who
is pursuing a career in international relations. “On the internet, I feel I have
lost that control.”
Machine Learning Reimagines the Building Blocks of Computing
In addition to performance gains, the field also advances an approach to
computer science that’s growing in popularity: making algorithms more efficient
by designing them for typical uses. Currently, computer scientists often design
their algorithms to succeed under the most difficult scenario — one designed by
an adversary trying to stump them. For example, imagine trying to check the
safety of a website about computer viruses. The website may be benign, but it
includes “computer virus” in the URL and page title. It’s confusing enough to
trip up even sophisticated algorithms. ... And this is still only the beginning,
as programs that use machine learning to augment their algorithms typically only
do so in a limited way. Like the learned Bloom filter, most of these new
structures only incorporate a single machine learning element. Kraska imagines
an entire system built up from several separate pieces, each of which relies on
algorithms with predictions and whose interactions are regulated by
prediction-enhanced components.
Microsoft has demonstrated the underlying physics required to create a new kind of qubit
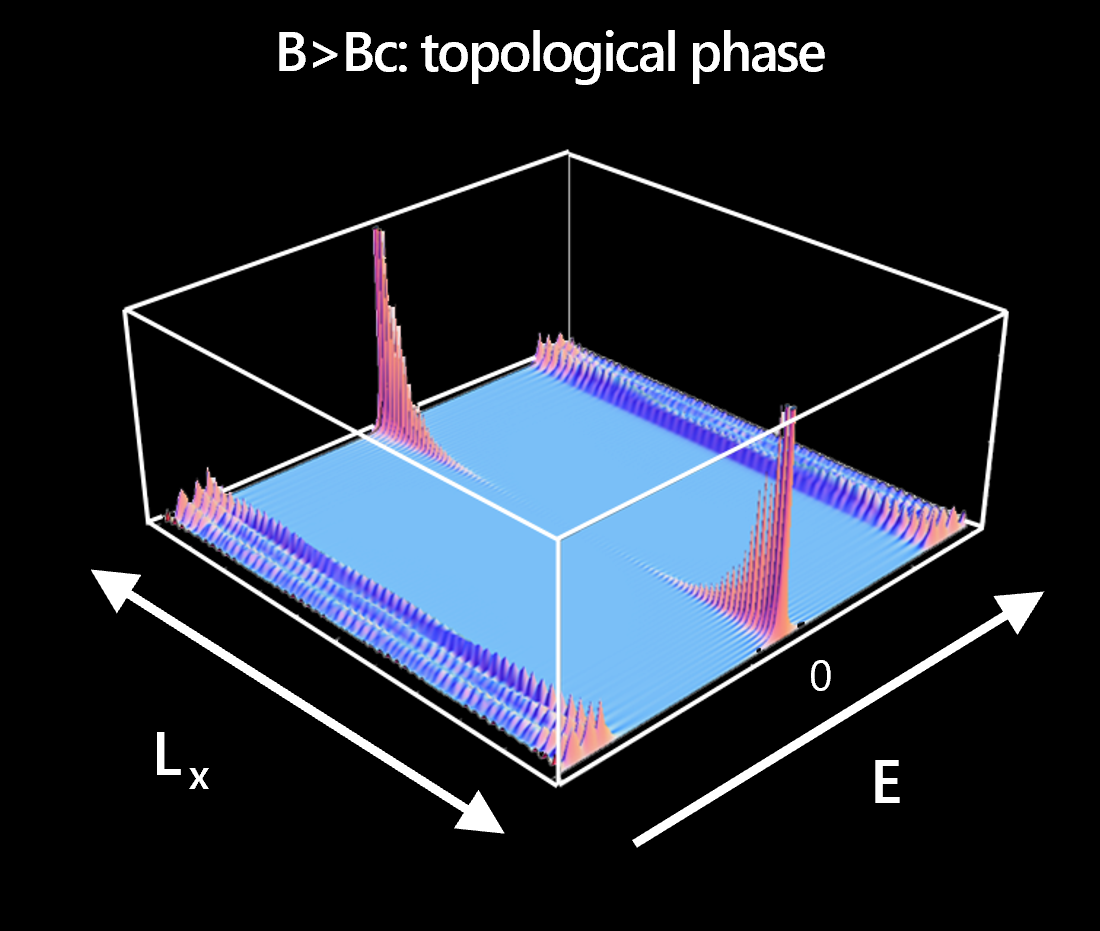
After a two-year hiatus of in-person meetings due to the pandemic, the Station Q
meetings resumed in early March. At this meeting with leaders in quantum
computing from across industry and academia, we reported that we have multiple
devices that have passed the TGP. Our team has measured topological gaps
exceeding 30 μeV. This is more than triple the noise level in the experiment and
larger than the temperature by a similar factor. This shows that it is a robust
feature. This is both a landmark scientific advance and a crucial step on the
journey to topological quantum computation, which relies on the fusion and
braiding of anyons (the two primitive operations on topological quasiparticles).
The topological gap controls the fault-tolerance that the underlying state of
matter affords to these operations. More complex devices enabling these
operations require multiple topological wire segments and rely on TGP as part of
their initialization procedure. Our success was predicated on very close
collaboration between our simulation, growth, fabrication, measurement, and data
analysis teams.
Break the master-slave IT partnership with a co-creation strategy

Indulging into an IT partnership is similar to adopting a new business paradigm.
Whilst IT leaders are keen for innovation it must be recognised that nurturing
inclusivity can provide rapid growth in innovation. In order to bolster
inclusivity, businesses can include employees from the partner teams within
project discussions and implement strategies that involve beneficial engagement
from both sides. Doing this not only can establish a positive inclusive culture,
but also generate a variety of opinions that can lead to better decision-making.
An imperative factor to note is that the process of building an inclusive
culture is not a one-time thing; rather it is an ongoing practice that needs to
be embedded within the workplace culture. Open and transparent communication
with a human-to-human approach can enable IT partners to understand each other’s
perspectives on any project and allow them to put their thoughts before others.
This exchange of thoughts, opinions and suggestions can promote inclusivity in
the workplace that can further strengthen the IT partnership.
Senators Request Briefing on Infrastructure Cybersecurity
The group led by Rosen and Rounds commends CISA's recently published "Shields
Up" technical guidance webpage to help organizations prepare for, respond to
and mitigate the impact of cyberattacks stemming from the conflict in Eastern
Europe. Last month, CISA first issued the "Shields Up" warning to U.S.
organizations, urging basic but crucial cyber hygiene measures that must be
addressed in the face of a potential surge in Russian state-backed cybercrime.
CISA and the FBI also subsequently warned of specific wiper malware targeting
Ukrainian organizations. The nation's operational cyber agency issued the
advisory as denial-of-service and malware attacks began surfacing last month.
CISA said at the time that it had been working hand in hand with partners to
identify and rapidly share information about malware and other threats. The
agency also warned that Russian cyber actors could seek to exploit existing
vulnerabilities to gain persistence and move laterally.
Multimodal Bottleneck Transformer (MBT): A New Model for Modality Fusion
Transformer models consistently obtain state-of-the-art results in ML tasks,
including video (ViViT) and audio classification (AST). Both ViViT and AST
are built on the Vision Transformer (ViT); in contrast to standard
convolutional approaches that process images pixel-by-pixel, ViT treats an
image as a sequence of patch tokens (i.e., tokens from a smaller part, or
patch, of an image that is made up of multiple pixels). These models then
perform self-attention operations across all pairs of patch tokens. However,
using transformers for multimodal fusion is challenging because of their
high computational cost, with complexity scaling quadratically with input
sequence length. Because transformers effectively process variable length
sequences, the simplest way to extend a unimodal transformer, such as ViT,
to the multimodal case is to feed the model a sequence of both visual and
auditory tokens, with minimal changes to the transformer architecture. We
call this a vanilla multimodal transformer model, which allows free
attention flow (called vanilla cross-attention) between different spatial
and temporal regions in an image, and across frequency and time in audio
inputs, represented by spectrograms.
Why a modern vulnerability management strategy requires state-of-the-art solutions
Vulnerability management technology has evolved significantly in recent
years, and state-of-the-art vulnerability management solutions are required
to implement an effective and efficient vulnerability management plan in the
modern enterprise. For starters, vulnerability identification requires a
“best of breed” approach to vulnerability scanning tool selection.
Vulnerability scanning vendors specialize in vulnerability identification
for different layers of the technology stack, and it isn’t uncommon to have
a dozen or more scanning tools in use through the organization to identify
vulnerabilities in computing devices, networks, custom code, third party
libraries, cloud configurations, APIs, database technologies, SaaS products,
and more. Given the vast number of vulnerability scanning and identification
tools typically in use throughout the enterprise, a vulnerability
aggregation capability and centralized vulnerability database is key to
implementing a consistent vulnerability response methodology across the
organization.
Quote for the day:
"Leaders who won't own failures
become failures." -- Orrin Woodward
No comments:
Post a Comment