This new startup aims to make developers love security

The accelerating speed of development teams and the failings of traditional perimeter and agent-based security solutions in cloud-native environments. With regard to the first trend, writes Vadlamani: It allows engineers to specify their infrastructure composition in a declarative language, allowing them to use the same versioning and release management workflows as for their source code. It greatly simplifies the work associated with deployment, testing and rollbacks. It allows them to be truly agile, spinning up new services in rapid succession to respond to changing business needs, and massively reduces the "busy work" associated with setting up the right environment and providing the runtime for their software. While that's great for development, it potentially creates new security issues that traditional security solutions are a poor fit to solve. Even the best security teams may struggle with threat detection and incident response in this cloud-native world. Perimeter defenses don't really work in this environment. In addition, it's difficult to deploy agents across these new ephemeral solutions, and requires security teams to manually manage changing policies, certify deployments, and respond to alerts.
Microsoft discovers new sLoad 2.0 (Starslord) malware

According to a Microsoft report from December 2019, sLoad had become one of the few malware strains that ported its entire host-server communications systems to the Windows BITS service. For those unfamiliar with the term, Windows BITS is the default system through which Microsoft sends Windows updates to users all over the world. The BITS service works by detecting when the user is not using their network connection and utilizing this downtime to download Windows updates. But the BITS service is not entirely reserved for the Windows Update process. Other apps can tap into BITS and use it to schedule tasks and network operations to take place when the computer's network connection goes idle. The sLoad authors appear to be some of the biggest fans of this service. Microsoft says that the malware's entire network stack was configured to work via the Windows BITS service of an infected host. The malware would set up BITS scheduled tasks that would execute at regular intervals. These tasks would be used to talk with its C&C server, download secondary malware payloads, and even send data from an infected host back to the C&C server
AI Will Give Rise To FinTech 2.0 And Longevity Banks
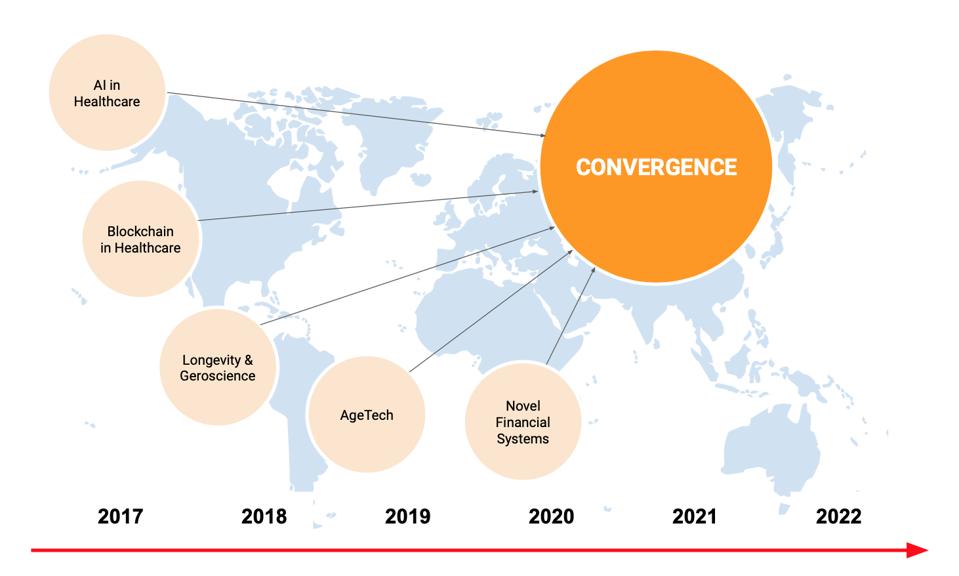
In the next few years, age-friendly FinTech companies and Longevity Banks will develop new financial products designed for clients who are planning to live extra long lives and want to remain high functioning and financially stable throughout. Clients of Longevity Banks will have more time to accumulate wealth, will have a longer investment horizon, and will benefit from compounding. Financial services innovators have an opportunity to enhance the financial lives of a billion people by designing new solutions and adapting existing products and services. ... The Longevity AI Consortium at King’s College London is developing sophisticated methods for translating advanced AI for Longevity solutions including novel applications of life data for insurance companies, pension funds, healthcare companies, and government bodies. This year the Consortium is planning to expand to Switzerland, Israel, Singapore, and the US. Progressive investment banks, pension funds, and insurance companies are developing new business models, and are using AI to improve the quality of the analytics used to formulate them.
How Google’s influence on AI is becoming key to business success

Google is the obvious version of that, especially as they’re so far ahead, but some of the good practices we can adopt to make things better for Google, such as consistency and clean, structured data) will be useful throughout business transformations. The past decade alone has seen huge leaps in Google’s capabilities and focus on AI, with the arrival of Google Assistant in 2016 and the Neural Matching algorithm introduced in 2018, to deliver more diverse search results by analysing language on a deeper level than previous algorithms. For the first time, Google could match words to concepts and figure out what a user wanted from a looser search. Google’s commitment only looks set to grow, with the company’s co-founder, Larry Page, taking a particularly close interest in AI, revealing that: “Google will fulfil its mission only when its search engine is AI-complete.” Google is definitely, absolutely committed to AI. Larry Page is committed, and it is viable in both short-term, by being able to out-analyse competition, and the long-term, the consequences of being the first creator of anything resembling true AI is vast.
A brave new workless world

Daniel Susskind, an Oxford professor and former government advisor, believes that work “is so entrenched in our psyches that there is often an instructive resistance to contemplating a world with less of it, and an inability to articulate anything substantial when we actually do.” His argument in A World without Work, a useful and farsighted book on the subject, is threefold: that within our lifetime, automation will result in insufficient work to go around; that this structural technological unemployment, if ignored, would make our already unfair world vastly more unequal; and that to prevent this outcome, governments’ approach to labor policy needs to be entirely rethought. Of these three strands, Susskind’s first is his most convincing. To be sure, he acknowledges, workers have regularly panicked unnecessarily about being replaced by machines. But this time, he argues, the threat is real. His best evidence of the frightening pace at which AI is developing comes through attempts to build robots to play chess and Go. For years, scientists followed an approach of trying to copy human thought and behavior.
The Human Screenome Project will capture everything we do on our phones
One of the biggest obstacles to the project’s success is likely to be that it raises fears around privacy. Having an app quietly record your activity every five seconds is a hard sell. If the past few years have shown anything, it’s that even the most inane activities online are tracked. That information is sold to advertisers at best, or to hackers and disinformation campaigns at worst. The Cambridge Analytica scandal highlighted how personality tests shared between acquaintances on Facebook were weaponized by Russians in the 2016 American election, for example. And consider what passes across our phone screens every day: bank account information; emails carrying personal data; car-sharing routes detailing addresses of destinations; meal delivery orders; texts with our loved ones; photos and videos of children; even pornography, cryptocurrency exchanges, and illicit activity. “It’s a lot of sensitive information,” Reeves concedes. His team has amassed around 30 million screenshots from volunteers in the US as well as China and Myanmar.
Modern Android App Architecture with JetPack and Dropbox Store

Dropbox recently took ownership of the open-source Store library to revamp it and bring it closer to the current Android developer ecosystem. Originally developed at the New York Times, Store has been rewritten in Kotlin on the foundations provided by Coroutines and Flow. Along with Google JetPack collection of libraries, Dropbox Store provides a solution to create modern Android apps. When Google introduced JetPack, it set an ambitious goal for it: accelerating development of high-quality apps for the Android platform. Two key ideas drove the design of JetPack towards that goal. On the one hand, JetPack aims to leverage advanced Kotlin features to reduce boilerplate code programmers had to write. On the other hand, it also provides higher-level abstractions on top of those found in the Android SDK, such as Fragments and Activities, to allow them to express complex tasks in a simpler way. JetPack includes a number of components that can be used independently on one another and cover four main concern areas: Foundation, Architecture, Behavior, and User Interface, as shown in the following image.
How remote work rose by 400% in the past decade

The report found that the rise of remote work popularity is thanks to the evolution of supporting technologies including powerful mobile devices, ultra-fast internet connections, and proliferation of cloud-based storage and SaaS solutions. "The rise of cloud-based SaaS software has been instrumental to the growth of remote work," de Lataillade said. "Employees can now instantly connect and collaborate with colleagues around the world at any time." Employees definitely took advantage: The majority (78%) of employees said they work remotely some of the time; more than half (58%) said they work remotely at least once a month; and, 36% of respondents said they work remotely at least once a week, the report found. While 36% might not seem like a huge percentage, it's a significant jump from 10 years ago. In 2010, the US Census Bureau found that only 9.5% of employees worked remotely at least once a week, indicating that the number of people working remotely on a weekly basis has grown by nearly 400% in the last decade, according to the report.
Microsoft and Google just can't agree on proposed ban on facial recognition

Speaking at a conference in Brussels on Monday, Pichai said it was important for governments to tackle regulatory questions over facial recognition and, more broadly, AI "sooner rather than later", and that the ban can be "immediate but maybe there's a waiting period before we really think about how it's being used". ... "Accountability is an important part of our AI principles. We want our systems to be accountable and explainable and we test it for safety," Pichai told the thinktank Bruegel, which organized the conference. "I think inevitably doing that we assume it will involve human agency and humans to review it, and we specifically mention we want these systems to be accountable to society at large. And I think regulation should play a role in that as well." The European Commission acknowledges in its proposal that a temporary ban on facial recognition would "be a far-reaching measure that might hamper the development and uptake of this technology", therefore it would prefer to use existing regulatory instruments available under GDPR.
The Role of Developers in Digital Transformation

Firstly, efficient code delivered in a timely manner should be the goal of every developer. Testing and QA will, of course, reveal issues, and no one is perfect, but developers must be mindful of the impact inefficient or inaccurate code can have on a business. Workarounds may get you past a problem, but this is not best practice and leaves the business exposed should a client pick up on it–especially if the workaround causes more serious issues further down the line. Fewer bugs or defects means scrum meetings can naturally focus more on strategy and new initiatives that might help grow the business. Organizations should therefore establish best practices and coding guidelines to reduce the temptation for workarounds, ensuring code releases are reliable and ready for the production environment. Developers must also be able to comprehend the requirement to work with designs given to them by design teams, as these will align with customer expectations. Being able to dynamically incorporate client feedback into the development process is also key, particularly for those working with continuous delivery and continuous integration pipelines.
Quote for the day:
"Everyone carries a bucket of water and a bucket of gas in life. A leader has learned to throw the right one at the right time." - Orrin Woodward
No comments:
Post a Comment