Blockchain/IoT integration accelerates, hits a 'sweet spot'

Blockchain acts as an automated communication layer between IoT sensors as well as a repository for the data they produce and upload. For example, IoT devices in shipping containers can track not only location but monitor temperature, vibration and whether a package has been tampered with. Earlier this year, FedEx touted a proof of concept involving "sensor-based logistics," using two types of IoT sensors about the size of a stick of gum. One acts as a geo-sensor, the other automatically transmits data to a blockchain ledger. Gartner is not alone in seeing a lot of activity related to IoT and blockchain. Last month, UK-based Juniper Research said in a report that the use of blockchain and IoT tracking technology will "revolutionize" the food industry, reducing food fraud by $131 billion in five years. Currently, food-tracking systems rely on paper-based transactions to manually track goods throughout a supply chain, an inefficient system that allows records to be lost or unreconciled, according to Juniper analyst Morgane Kimmich. Additionally, paper-based records cannot be shared by all supply chain users, hindering visibility into the supply chain.
The rise of a digital underclass may be tech's next big challenge

"Any organization processing data is required to let people access this data and rectify it if necessary," she said. "But most people don't exercise those rights "We can't have safeguards only for those who have the time, expertise and money to understand what they are entitled to by law." For her, the solution lies in accountability – "because accountability means that organizations have to consider the risk that data processing poses for people," she said. A successful step forward, she said, was the implementation of GDPR. With accountability featuring among its key principles, GDPR warns organizations that they are responsible for putting in place appropriate technical measures to meet the requirements of data protection. For example, corporations may have to implement privacy-by-design, which requires tech companies to develop software that makes privacy the default mode of operation. While accountability is at the heart of GDPR, however, there is still reason to be skeptical that the new European rules will be enough to change the whole game.
GraphQL: The Future of APIs
A pre-defined schema is offered to clients by the GraphQL server. This is basically the model data that can be retrieved from the server where the schema acts as the connector between the server and the client whilst defining the process of accessing the information. The basic elements of a GraphQL schema are written down in SDL or Schema Definition Language. It explains all sorts of objects that can be requested on that specific server including the fields that they possess. The queries that are permitted to be requested such as what types of data can be fetched and the relationships between these types are defined by the schema. In fact, the GraphQL schema can be developed and an interface can be created around it with any programming language. To make sure that the server is able to respond to the query, the client can validate their query against the schema. You will be able to predict the outcomes depending on the shape of the GraphQL query that closely resembles the result. This additionally scrubs out any unwelcome surprises, for example, incorrect structure or unavailable data.
Passive optical LAN: Its day is dawning
The increased speeds pose quite a predicament for companies. If the organization has Cat5 cabling, the speed is capped at 1Gbps. If Cat6 is deployed, speeds of 10Gbps can be reached but only 55 meter’s distance. If the company wants to reach the full 100M length of copper, Cat6A or higher must be used. Optical cable has no distance limitations because POL is completely passive and requires no electronics to boost the signal. Optical cabling can carry petabytes of bandwidth over long distances. Also, with optical, there’s no concern over what type of cable is being used and having the quality degrade over time. ... The project features an optical network built on Huawei’s Campus OptiX solution that simplifies the network as the architecture moves from a three-tier hierarchical design to a two-tier one. That design uses less equipment and reduces power and cooling requirements. Also, the flat, 10Gbps network obviates the need for parallel overlay networks, making it easier to manage and giving it a degree of future-proofing as the network can easily be upgraded. The all-optical network resulted in a 60% improvement in operational efficiency and a deployment time that was cut in half compared a similar network using Ethernet.
Cracking the Code to Mobile Productivity
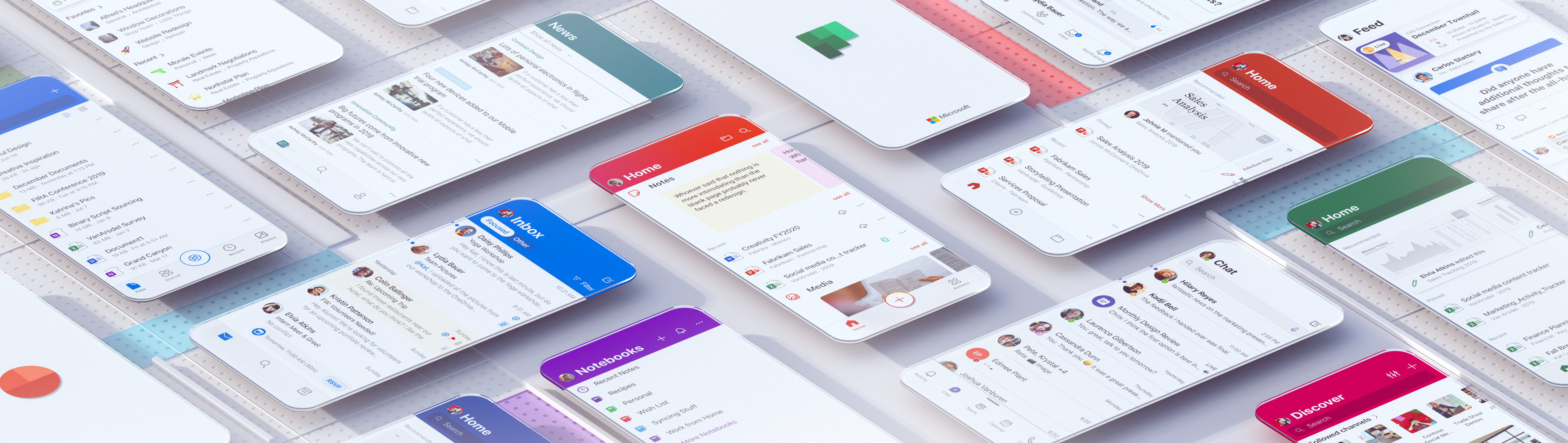
Human-centered research underpins great design, and our teams dove deep to understand how people think, feel, and act when getting things done on the go. Research in mobile-first or mobile-only markets like India and China allowed us to study everyone from students to factory floor workers. We also leveraged pioneering work by Jaime Teevan and Microsoft researchers around “microproductivity.” Microproductivity exemplifies meeting users where they’re at: the modern world has increasingly fragmented work. Instead of solely pushing people to focus more, however, we explored whether those fragmented slices of time could be more productive with “microtasks.” A microtask is a bite-sized piece of a bigger task, like writing one paragraph instead of working on an entire Word document. Research showed microtasks increase feelings of productivity. This aligned with our observations of mobile behavior where, despite spending up to four hours a day on the phone, sessions average just 20 to 30 seconds.
5 Mobile App Design Trends You Should Know for 2020

Whenever a popular device or app moves to the dark side (i.e. Dark Mode), it’s always big news. Apple just recently enabled the feature on its iPhones in October of 2019. Instagram added it around the same time, too. People went nuts for it. ... One could argue that mobile apps are much easier to use than websites that are overloaded with content. However, the assumption that mobile users know what to do when they first enter an app or even that they understand the real value of it can be problematic. Because if you feel like the app is a no-brainer, then you’re going to design it that way, which may prevent some users from ever really knowing how much they can do with it. Since you don’t have the luxury of sharing as much information with users as your PWA counterparts do, I think swipeable intros are the solution. We’re starting to see a number of apps utilize these before ever inviting users to sign up or log in and I think more apps will adopt this friendlier approach to onboarding users in the years to come.
CorePlus: A Microsoft Bot Framework v4 Template
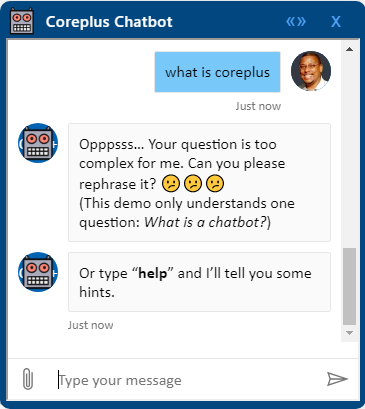
Microsoft has developed a number of samples to help you get started with the Bot Builder SDK v4, as well as a set of templates powered by the scaffolding tool Yeoman. This article introduces CorePlus, a Microsoft Bot Framework v4 template that I have created, based on a previous version of the Core Bot template (Node.js) supported by the generator-botbuilder Yeoman generator. It's an extended and advanced version, intended as a quick-start for setting up a Transactional, Question and Answer, and Conversational chatbot, all in one, using core AI capabilities. The template proposes a modified project structure and architecture, and provides solutions for the technical and design challenges that arise. Although some basic knowledge on Microsoft Bot Framework: Node.js SDK, LUIS, QnA Maker, Bot Framework Emulator, etc., is recommended, it's not required. The code is fully commented and the article provides lots of external links to samples, documents and other articles that can help you expand your vision and knowledge on Microsoft's framework as well as on chatbots design and development in general. Visual Studio Code is suggested as the code editor of choice. You may use any other one of your preferences, though, such as WebStorm.
Microsoft details the most clever phishing techniques it saw in 2019

The first is a multi-layered malware operation through which a criminal gang poisoned Google search results. The scheme went as follows: Crooks funneled web traffic hijacked from legitimate sites to websites they controlled; The domains became the top Google search result for very specific terms; Phishers sent emails to victims linking the Google search result for that specific term; If the victim clicked the Google link, and then the top result, they'd land on an attacker-controlled website; and This website would then redirect the user to a phishing page. One might think that altering Google search results takes a gigantic amount of effort, but this was actually pretty easy, as attackers didn't target high-traffic keywords, but instead focused on gibberish like "hOJoXatrCPy." ... A third phishing trick that Microsoft wanted to highlight as a clever phishing attack this year was one that made use of a man-in-the-middle (MitM) server. Microsoft explains:"One particular phishing campaign in 2019 took impersonation to the next level.
The Future of APIs and API Monetization

First, the future API stack is secure. There is a lot of information and prioritization around cybersecurity and endpoint security, but sometimes API endpoints are overlooked. While OAuth is not new, the use of OAuth is essential to control fine-grained access to APIs. Second, APIs must enable personalization and experimentation. Companies need the ability to control and test API capabilities so that we can personalize search results as easily as we personalize user experience. We continuously experiment with search rankings and results to better serve our sellers and buyers. eBay is a search-driven marketplace. APIs must be designed so they can support personalization and experimentation. Third, the future API stack must be device-agnostic. APIs should understand if they are talking to a desktop or mobile device, or communicating across limited bandwidth, and adjust the fidelity of their responses accordingly. If your client pulls data from a massive data center over a LAN connection, it’s probably fine for APIs to allow access to several GBs of data.
How to develop IT leaders into future CIOs

Every IT leader reaches an inflection point where they have to become very good at team leadership if they want to take on more responsibility. The ability to lead and not do is more important to the CIO role than technical depth. If you don’t start to develop those skills early in your career, you will fail as a CIO. This is not about delegation, which is just handing a task off to someone else. Leadership is about empowerment and trust. ... There are a number of ways, including getting your MBA or finding a mentor who is a leader in a business function that is not IT. Early in my career, I held finance, HR and customer service roles, which had a technology flavor to them, but were not in IT. Future CIOs should get that cross functional experience early in their careers because it is harder to move in and out of IT as you advance. Understand also that sometimes you have to take a step backward to move forward. You might have to drop down a level for roles in finance or supply chain, but that move will allow you to advance later in your career.
Quote for the day:
"Do all the good you can. By all the means you can. In all the ways you can... At all the times you can." -- John Wesley
No comments:
Post a Comment