
One of the first (and biggest) warning signs that your project may be headed for failure is an internal culture that is resistant to change. Projects bring about improvements in workflows and new operational best practices, often with an increased use of technology. These changes can create a significant amount of fear, as employees assume the end result will mean job losses or major disruption to their individual working world. Many projects have been internally sabotaged right from the start as result of these fears. How can you tell if you have a culture that is resistant to change? Employees who are resistant to change are often reluctant to share information and exhibit negative attitudes towards the project and its benefits, either through direct communication or body language and facial expressions. Alleviating these fears by creating a culture that embraces change is key.
A quick-and-dirty way to predict human behavior

Machine learning and AI technologies are everywhere. One of the top uses is to predict human behavior. Luckily, people are creatures of habit. Moreover, when given the freedom to do anything they want, most people will do what everyone else is doing (I’m paraphrasing a badly remembered quote). That makes is kind of easy to predict what people will do next, at least statistically. Imagine you go to a website and start rating things. First you rate a cat picture, then a baseball, and then a Magpul FMG-9. There were also a few things you didn’t rate on the same page. Assuming that someone else made similar rankings as you, we can probably “guess” what you’d rank the other things. ... The algorithm that many recommendations are based on is called Alternating Least Squares (or some form of it). With ALS, you use a training set or, if you have a lot of users, you can use some of them as the training set to rate the others.
HP expands its Device-as-a-Service offering to include Apple

Through its DaaS offering, HP determines the contractual relationship enterprises want to have, whether it's with a value-added reseller, a global systems integrator or a direct relationship with HP, "and then we provide it back to you within a utility model or a per-user, per-device pricing model," said Jonathan Nikols, global head of HP's Device-as-a-Service. For example, the cost of a contract would include an SLA on how fast the turnaround time on a device repair and replacement should be – whether it's next day or in four days. When an end user's device breaks or needs replacing, they file a help-desk ticket just as they would with any IT shop; the ticket is automatically routed to the HP DaaS service. The service also handles employee on-boarding and off-boarding. Mixed-device environments are the norm now, HP said, making it increasingly difficult and costly for organizations to manage multiple device types, OSes and vendors.
Who should buy a Ryzen APU, and who shouldn't
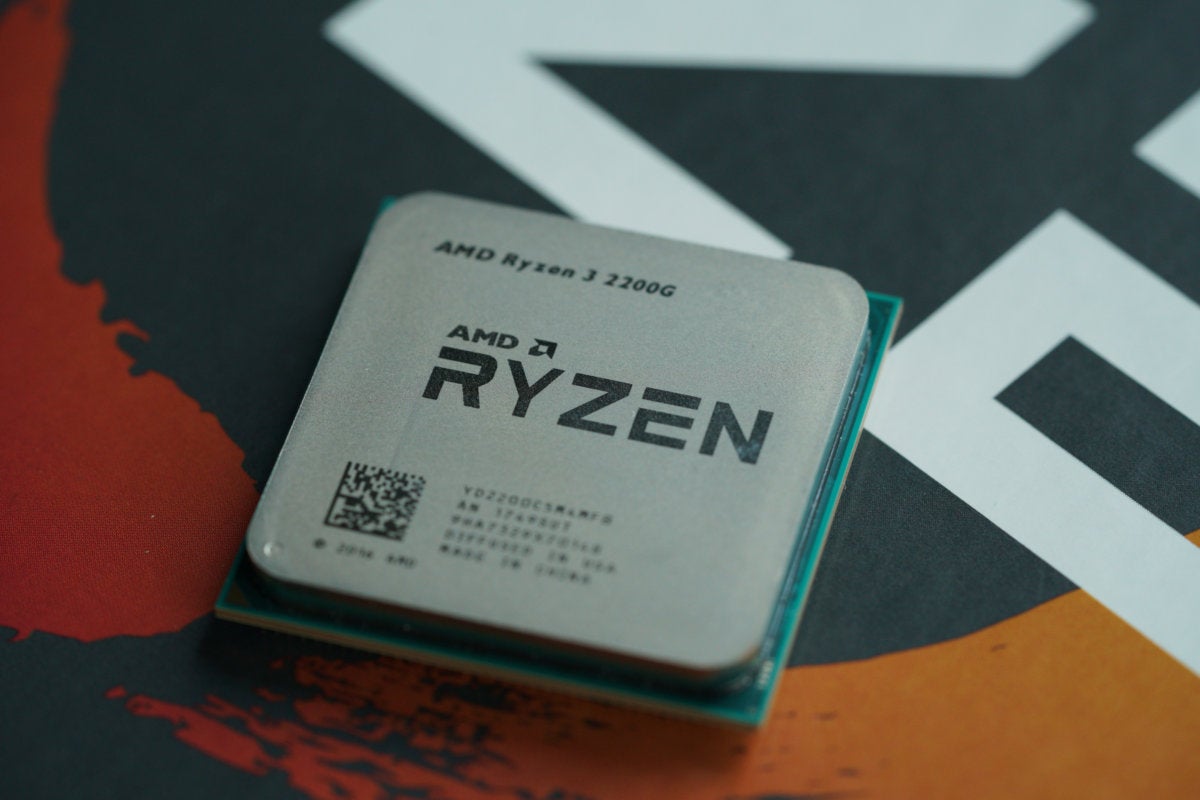
If you're asking yourself, "should I buy a Ryzen APU?" for a new budget gaming PC, the short answer is yes, probably. That's because for building a ground-up, entry-level gaming machine, the Ryzen APU is the best game in town, and possibly the only game for DIY builders, in the face of wallet-busting GPU prices. But for everyone? Well, no. There is no one-size fits all answer, so read on to learn who should buy the Ryzen APU—and who shouldn't. ... AMD's new APUs have essentially enough CPU and GPU power to enable satisfying gaming at 720p to 1080p. Both APUs combine quad-core Zen x86 cores with up to 11 Vega graphics cores, and the Ryzen 5 2400G also has SMT. The integrated graphics basically offers from double to triple the gaming performance of Intel's HD 630 graphics, which is inside everything from an $85 Pentium to a $380 Core i7.

As any executive whose company has suffered a data breach knows, the true costs of cybercrime are devastating, far-reaching and continue long after business functions have been restored. Between investigation and repair costs, customer notification requirements, contractual liabilities and workflow continuity, worldwide spending to mitigate the impact of cyberattacks is projected to reach an unprecedented $90 billion this year. Then there are the indirect costs, which include legal fees and public reputation rebuilding. This last component is particularly crucial, since a recent Gemalto survey revealed that 70 percent of consumers said they would cut ties with a company that had suffered a cyberattack. Indeed, businesses are anticipated to bear the brunt of cybercrime’s growing financial burden.Over half of last year’s cyberattacks targeted corporations; and among all small businesses, 58 percent had been personally hit by data breach.
Juniper Networks Expands Portfolio for Secure Multicloud Computing

“The promise of multicloud is to deliver an infrastructure that is secure, ubiquitous, reliable and fungible and where the migration of workloads will be a simple and intuitive process,” said Bikash Koley, chief technology officer at Juniper Networks. “For IT to be successful in becoming multicloud-ready, it is critical organizations consider not only the data center and public cloud, but also the on-ramps of their campus and branch networks. Otherwise, enterprises will face fractured security and operations as network boundaries prevent seamless, end-to-end visibility and control.” A Juniper-commissioned study by PwC found that workload migration is underway in the next three years across every core functional area, such as customer service, systems management, marketing, compute bursting, business applications, DevOps and backup and recovery.
Bitcoin thieves use Google AdWords to target victims

The fraudsters established "gateway" phishing links that appeared in search results when potential victims searched Google for cryptocurrency-related keywords, such as "blockchain" or "bitcoin wallet." These links, bolstered by the purchase of Google AdWords, would then send victims to malicious domains, which would serve phishing content depending on the IP address and likely language of the visitor. According to the team, the hackers are focusing on countries where access to traditional banking may be difficult, such as Estonia, Nigeria, Ghana, and a number of other African countries. When access to banking is difficult, cryptocurrency, as decentralized assets recorded on the Blockchain, may empower users financially. However, it seems that the cybercriminals behind the campaign also know there may be more interest from residents of these countries, and so, this idea has decided the focus of phishing campaigns.
Google's Android P will make it easier for OEMs to copy iPhone X

Google's intent on making Assistant more visible in Android comes as the personal digital assistant market is becoming too crowded, forcing potential competitors out. While Amazon's Alexa and Microsoft's Cortana are available as downloadable apps, Samsung's built-in and much maligned Bixby assistant continues to linger, though The Verge has called for Bixby's death. Cortana was conspicuously absent at CES 2018, leading ZDNet's Larry Dignan to declare the trade show "Cortana's Funeral." Facebook announced the discontinuation of their virtual assistant, M, in January. For screen cutouts, it is yet to be seen if this design trend will continue to persist, or if this will wind up as a fad similar to 3D phones. While Apple's use of the technology is notable, it seems unlikely that manufacturers are holding back on shipping phones for lack of OS-level support. Of note, Sharp also produced a handful of 3D smartphones available primarily in Japan.
Nokia is re-evaluating its wearables division

Once a global leader in mobile, the company failed to embrace the smartphone revolution, selling to Microsoft, which then shuttered the whole thing entirely. Of course, the Nokia name is back in the smartphone space, but that comes under a licensing deal through HMD — a company founded by former execs from the company. Interestingly, recent numbers show that the brand has actually been doing pretty well. Wearables, on the other hand, have stagnated, forcing brands to exit the space, sell or shutter entirely. The herd has thinned over the past year, and even top names like Fitbit have struggled to keep their head above water. For Nokia, acquiring a company like Withings no doubt seemed like a quick way to hit the ground running — but the timing was rough on this one. Hopefully this doesn’t mark the end of the Withings/Nokia Health line, which made some really solid and innovative devices.
Cloud sync vs backup: Which disaster recovery works better for business continuity?
Backup is the traditional way most businesses protect their digital assets from disaster. At regular intervals, changes in local storage are transferred to either a local backup device or a cloud backup service. Usually, these changes are incremental and go into backup archives. A good backup service will store ongoing snapshots, so it's always possible to go back in time and recover an old document. The gotcha with backup systems is that recovery is often cumbersome. You usually have to launch a backup program on your PC, dig through the various backup instances, and initiate a restore. In most cases, you can't really use or read the files in the backups until they're restored to your computer. Cloud sync, by contrast, takes files that exist on your local computer and moves them into a cloud infrastructure. Most cloud infrastructures encourage you to work on the files in the cloud.
Quote for the day:
"A leadership disposition guides you to take the path of most resistance and turn it into the path of least resistance." -- Dov Seidman
No comments:
Post a Comment