Getting Started with Design Thinking for Developers and Managers
 More visual, intuitive types of designers do still sometimes struggle working
with developers; they expect developers to just accept their intuitive
conclusions. But developers in general don't go for touchy-feely intuitive
design. They want more logical reasons for design choices. Besides, true
design thinking goes beyond intuition, leveraging measurement and analysis
too. It's therefore generally a bad idea for a more intuitive, visually
oriented designer to lead a design team containing developers. While those
designers are valuable members of a design thinking team, their disconnect
with developers and their bias towards intuition over analysis means they
should not be running the show. ... Visual designers have a vested interest in
fostering that impression. Some developers are happy to go along with it
because it gives them an excuse to delegate any responsibilities concerning
design.It's also a simple and tangible concept for managers to get their heads
around. The visual nature is something they can see immediately. More
sophisticated forms of design take more effort to understand.
More visual, intuitive types of designers do still sometimes struggle working
with developers; they expect developers to just accept their intuitive
conclusions. But developers in general don't go for touchy-feely intuitive
design. They want more logical reasons for design choices. Besides, true
design thinking goes beyond intuition, leveraging measurement and analysis
too. It's therefore generally a bad idea for a more intuitive, visually
oriented designer to lead a design team containing developers. While those
designers are valuable members of a design thinking team, their disconnect
with developers and their bias towards intuition over analysis means they
should not be running the show. ... Visual designers have a vested interest in
fostering that impression. Some developers are happy to go along with it
because it gives them an excuse to delegate any responsibilities concerning
design.It's also a simple and tangible concept for managers to get their heads
around. The visual nature is something they can see immediately. More
sophisticated forms of design take more effort to understand.How Cybercriminals Are Operationalizing Money Laundering and What to Do About It
 Financial institutions, cryptocurrency companies, and other organizations face
increasing fines — sometimes ranging in the millions and billions of dollars —
for failure to root out money laundering as government agencies and regulators
worldwide seek to crack down on this scourge. ... A preferred tactic by
cybercriminal organizations looking to grow their ranks is to use what are
known as money mules. These are individuals who are brought in to help launder
money — sometimes, unknowingly. They're often lured in under false pretenses
and promises of legitimate jobs, only to discover that "job" is to help
launder the profits from cybercrime. Back in the day, this money shuffling was
typically done through anonymous wire transfer services. While they often got
away with it, such transfers are far easier for law enforcement and regulators
to track. These days, most criminals have moved to using cryptocurrency. Its
relative lack of regulatory oversight, coupled with often-anonymous
transactions, make it almost the ideal vehicle for money laundering.
Financial institutions, cryptocurrency companies, and other organizations face
increasing fines — sometimes ranging in the millions and billions of dollars —
for failure to root out money laundering as government agencies and regulators
worldwide seek to crack down on this scourge. ... A preferred tactic by
cybercriminal organizations looking to grow their ranks is to use what are
known as money mules. These are individuals who are brought in to help launder
money — sometimes, unknowingly. They're often lured in under false pretenses
and promises of legitimate jobs, only to discover that "job" is to help
launder the profits from cybercrime. Back in the day, this money shuffling was
typically done through anonymous wire transfer services. While they often got
away with it, such transfers are far easier for law enforcement and regulators
to track. These days, most criminals have moved to using cryptocurrency. Its
relative lack of regulatory oversight, coupled with often-anonymous
transactions, make it almost the ideal vehicle for money laundering. Solving Problems With The IoT
 Despite security concerns, the IoT is so useful that it continues to by leaps
and bounds — so much so that when ChatGPT, a new AI search engine, was asked
to list the top 100 applications for the IoT, the search engine simply added
the word “smart” in front of many common places and items. For example, it
responded with “smart aquariums, smart theme parks, smart libraries,” etc. Put
simply, the IoT is everywhere. What makes it so popular is its ability to
solve problems. For instance, safety is critical in manufacturing, industrial,
chemical processing, mining, and many other applications. IoT sensors can be
used to monitor environments for the presence of hazardous chemicals. If there
is a gas leak, a real-time alert can be sent to the control centers to prevent
potential accidents from occurring. In addition, aging infrastructure such as
bridges, buildings, highways, and power grids pose risks. To help mitigate
these risks, sensors in an IoT network can track cement movement and the
changing size of cement cracks. IoT monitoring of the moisture in some
building structures can provide advance warning of potential disasters such as
collapsing buildings and bridges.
Despite security concerns, the IoT is so useful that it continues to by leaps
and bounds — so much so that when ChatGPT, a new AI search engine, was asked
to list the top 100 applications for the IoT, the search engine simply added
the word “smart” in front of many common places and items. For example, it
responded with “smart aquariums, smart theme parks, smart libraries,” etc. Put
simply, the IoT is everywhere. What makes it so popular is its ability to
solve problems. For instance, safety is critical in manufacturing, industrial,
chemical processing, mining, and many other applications. IoT sensors can be
used to monitor environments for the presence of hazardous chemicals. If there
is a gas leak, a real-time alert can be sent to the control centers to prevent
potential accidents from occurring. In addition, aging infrastructure such as
bridges, buildings, highways, and power grids pose risks. To help mitigate
these risks, sensors in an IoT network can track cement movement and the
changing size of cement cracks. IoT monitoring of the moisture in some
building structures can provide advance warning of potential disasters such as
collapsing buildings and bridges.MoD issues revised cloud strategy as it prepares to move top-secret data off-premise by 2025
 The Department will be pursuing a multi-cloud approach to sourcing these
off-premise capabilities, because no one supplier will be able to address the
“complexity of Defence’s requirements” nor its “evolving ambition” or
scalability demands, according to the document. “By 2025, the services
required by game-changing military capabilities will be available across
Defence, accelerating our level of cloud consumption,” the document continued.
“We will take advantage of evergreen solutions to prevent future obsolescence,
and to ensure immediate access to the latest technologies, driving the pace of
modernisation. “By 2025, we will use cloud platforms as the foundation on
which to build capabilities in big data, advanced analytics, automation and
synthetics. We will spend the majority of our compute expenditure investing in
strategic modern platforms, rather than maintaining obsolete legacy
platforms.” Elsewhere in the document, the organisation said its aim is to be
“cloud-native” as much as possible, with members of the Defence community
encouraged to take an MODCloud-first approach to procuring services.
The Department will be pursuing a multi-cloud approach to sourcing these
off-premise capabilities, because no one supplier will be able to address the
“complexity of Defence’s requirements” nor its “evolving ambition” or
scalability demands, according to the document. “By 2025, the services
required by game-changing military capabilities will be available across
Defence, accelerating our level of cloud consumption,” the document continued.
“We will take advantage of evergreen solutions to prevent future obsolescence,
and to ensure immediate access to the latest technologies, driving the pace of
modernisation. “By 2025, we will use cloud platforms as the foundation on
which to build capabilities in big data, advanced analytics, automation and
synthetics. We will spend the majority of our compute expenditure investing in
strategic modern platforms, rather than maintaining obsolete legacy
platforms.” Elsewhere in the document, the organisation said its aim is to be
“cloud-native” as much as possible, with members of the Defence community
encouraged to take an MODCloud-first approach to procuring services.Google’s AI chatbot is out to rival ChatGPT
 While Bard is still in its early stages of development, Google is confident
that the system will be able to compete with ChatGPT and other AI systems in
the market. Apart from assisting with search engine capabilities, Bard will
bring other features that will assist developers in developing their
applications using Google’s language model. “Beyond our own products, we think
it’s important to make it easy, safe and scalable for others to benefit from
these advances by building on top of our best models,” Pichai wrote. “Next
month, we’ll start onboarding individual developers, creators and enterprises
so they can try our Generative Language API, initially powered by LaMDA with a
range of models to follow. Over time, we intend to create a suite of tools and
APIs that will make it easy for others to build more innovative applications
with AI.” For other end users, there has been a mixed reaction regarding how
AI chatbots will affect the order of things. While some people argue that the
advent of these chatbots and their potential integration into search engines
will aid the creative and marketing industries, others think otherwise.
While Bard is still in its early stages of development, Google is confident
that the system will be able to compete with ChatGPT and other AI systems in
the market. Apart from assisting with search engine capabilities, Bard will
bring other features that will assist developers in developing their
applications using Google’s language model. “Beyond our own products, we think
it’s important to make it easy, safe and scalable for others to benefit from
these advances by building on top of our best models,” Pichai wrote. “Next
month, we’ll start onboarding individual developers, creators and enterprises
so they can try our Generative Language API, initially powered by LaMDA with a
range of models to follow. Over time, we intend to create a suite of tools and
APIs that will make it easy for others to build more innovative applications
with AI.” For other end users, there has been a mixed reaction regarding how
AI chatbots will affect the order of things. While some people argue that the
advent of these chatbots and their potential integration into search engines
will aid the creative and marketing industries, others think otherwise.Yes, CISOs should be concerned about the types of data spy balloons can intercept
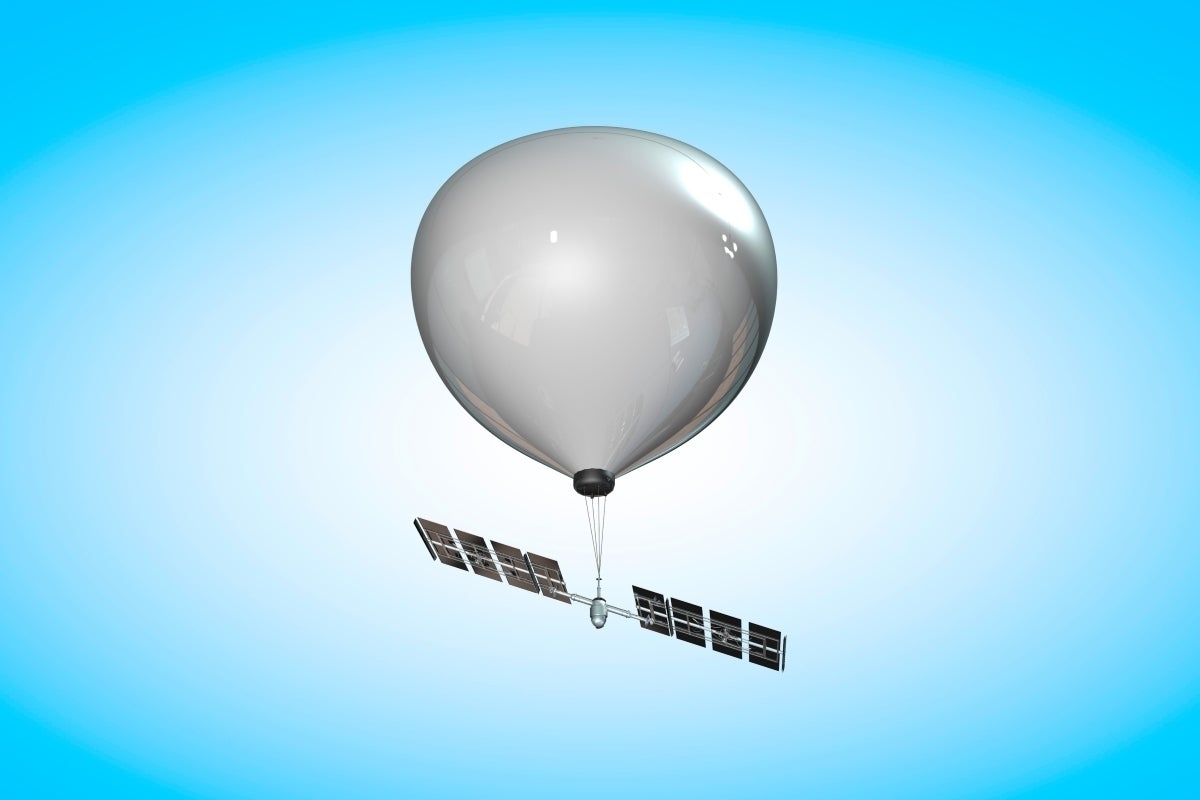 Nation-states will collect intelligence to further their knowledge of rivals
and a large part of that intelligence will come from private corporations. The
fact that China chose this particular time to do so is indicative of its
desire to place the United States in a weakened position ahead of a planned
visit to China by US Secretary of State Antony Blinken, if it could. The
United States didn’t take the bait and postponed the visit indefinitely and
sent a demarche to the government of China. The “sources tell us” snippets
from the mainstream media note that the United States purposefully allowed the
balloon and its collection platform to continue its mission and to receive
navigational commands but jammed the transmission of non-navigational signals.
Thus, it is probable that the Chinese tried to issue a destruct command (not
unlike those any CISO can do for a lost iPhone) but were unable to do so due
to US countermeasures. Regardless of the outcome of that technological duel in
the sky, the containers will provide valuable intelligence.
Nation-states will collect intelligence to further their knowledge of rivals
and a large part of that intelligence will come from private corporations. The
fact that China chose this particular time to do so is indicative of its
desire to place the United States in a weakened position ahead of a planned
visit to China by US Secretary of State Antony Blinken, if it could. The
United States didn’t take the bait and postponed the visit indefinitely and
sent a demarche to the government of China. The “sources tell us” snippets
from the mainstream media note that the United States purposefully allowed the
balloon and its collection platform to continue its mission and to receive
navigational commands but jammed the transmission of non-navigational signals.
Thus, it is probable that the Chinese tried to issue a destruct command (not
unlike those any CISO can do for a lost iPhone) but were unable to do so due
to US countermeasures. Regardless of the outcome of that technological duel in
the sky, the containers will provide valuable intelligence. 10 Tips for Developing a Data Governance Strategy
 There is no “one” right data governance leader. In some companies, the data
governance leader is the chief data officer. In others, it may be the CFO,
chief risk officer, or CIO. Historically, the role has resided within the
realm of IT. Today, that’s changing. A Forrester study found that 45% of
companies make data governance mostly business-focused, while 53% are
IT-focused. Forrester advises that data governance is more a business problem
and should be anchored in a business context. No matter which office heads up
the data governance strategy, the team should be spread throughout the
company, incorporating subject-matter or line-of-business experts, data
analysts, data scientists, the IT department, and legal counsel. “What we’ve
done wrong in the past is taken a role and turned it into a position, versus
thinking about how we use data, build insights, and make decisions from our
data,” Goetz said. “If you can see how you operate as a culture, you can
figure out who should own it in the company.”
There is no “one” right data governance leader. In some companies, the data
governance leader is the chief data officer. In others, it may be the CFO,
chief risk officer, or CIO. Historically, the role has resided within the
realm of IT. Today, that’s changing. A Forrester study found that 45% of
companies make data governance mostly business-focused, while 53% are
IT-focused. Forrester advises that data governance is more a business problem
and should be anchored in a business context. No matter which office heads up
the data governance strategy, the team should be spread throughout the
company, incorporating subject-matter or line-of-business experts, data
analysts, data scientists, the IT department, and legal counsel. “What we’ve
done wrong in the past is taken a role and turned it into a position, versus
thinking about how we use data, build insights, and make decisions from our
data,” Goetz said. “If you can see how you operate as a culture, you can
figure out who should own it in the company.”Cyber Insurance Costs Lead to Scrutiny of Business Partners
 “Many suppliers to large companies often are small businesses that lag behind
in their deployment of cybersecurity controls. They can be an easy path for
cyber criminals to launch attacks on larger organizations,” she says. “This
additional risk needs to be considered when pricing cyber coverage and has an
impact on cyber insurance premiums.” She explains that having adequate
cybersecurity deployed when interacting with third-party vendors drastically
improves the risk profile of any organization. “It also makes it more
insurable for cyber, which in return lowers premiums or opens more coverage
options,” Dumont adds. This approach by larger businesses ranges, for example,
from compliance to security best practices when deploying cloud providers and
requiring multi-factor authentication (MFA) for maintenance services when they
access the company’s connected equipment. From her perspective, third-party
scrutiny on cybersecurity yields positive outcomes for all, starting with the
most important benefit, which is to lower the likelihood of facing a cyber
incident.
“Many suppliers to large companies often are small businesses that lag behind
in their deployment of cybersecurity controls. They can be an easy path for
cyber criminals to launch attacks on larger organizations,” she says. “This
additional risk needs to be considered when pricing cyber coverage and has an
impact on cyber insurance premiums.” She explains that having adequate
cybersecurity deployed when interacting with third-party vendors drastically
improves the risk profile of any organization. “It also makes it more
insurable for cyber, which in return lowers premiums or opens more coverage
options,” Dumont adds. This approach by larger businesses ranges, for example,
from compliance to security best practices when deploying cloud providers and
requiring multi-factor authentication (MFA) for maintenance services when they
access the company’s connected equipment. From her perspective, third-party
scrutiny on cybersecurity yields positive outcomes for all, starting with the
most important benefit, which is to lower the likelihood of facing a cyber
incident.Seven deadly sins of devising a cloud strategy
 Relying on a single vendor to implement a cloud strategy is an inflexible
approach that leaves enterprises isolated when it comes to maintaining control
over the performance of their digital platform. It can mean having little or
no say in which services and providers can be adopted while being locked-in to
lengthy service agreements, even when prices rise, or when service levels fall
off. This is particularly pertinent given the dramatic reduction in the cost
of cloud services in recent years. ... Losing track of costs is easily done
when implementing a cloud strategy, especially in cases when the scale of the
transformation is significant. It’s imperative to identify areas where
resources are being mismanaged and then eliminate waste. For example, in a
sector such as financial services, which has traditionally been slow to adopt
cloud computing, taking a “rightsizing” approach will help identify areas that
have not been provisioned correctly. They can then be reconfigured to optimal
levels. In practice, this means only purchasing cloud services that a business
actually needs and that it will use.
Relying on a single vendor to implement a cloud strategy is an inflexible
approach that leaves enterprises isolated when it comes to maintaining control
over the performance of their digital platform. It can mean having little or
no say in which services and providers can be adopted while being locked-in to
lengthy service agreements, even when prices rise, or when service levels fall
off. This is particularly pertinent given the dramatic reduction in the cost
of cloud services in recent years. ... Losing track of costs is easily done
when implementing a cloud strategy, especially in cases when the scale of the
transformation is significant. It’s imperative to identify areas where
resources are being mismanaged and then eliminate waste. For example, in a
sector such as financial services, which has traditionally been slow to adopt
cloud computing, taking a “rightsizing” approach will help identify areas that
have not been provisioned correctly. They can then be reconfigured to optimal
levels. In practice, this means only purchasing cloud services that a business
actually needs and that it will use.Secure Delivery: Better Workflows for Secure Systems and Pain-Free Delivery
When reviewing architecture at a high level, any security concerns are usually big-ticket items that require considerable effort to retrofit, and sometimes even the redesign of a critical feature of a system like authentication. Lower-level threats and vulnerabilities are often found by outsourcing deeper technical security knowledge from an external penetration testing company, who are engaged to attack the system and highlight any serious issues. After these activities are complete, we usually see a fractious negotiation around risk and resources, with the engineering team pushing back on making expensive, time-consuming changes to their system architecture and operational processes just before their release deadlines, and the system owner pushing for risk acceptance for all but the most serious risks. Overall, security can be seen as something that’s owned by the security team and not an attribute of a system’s quality that’s owned by engineers, like performance or reliability.Quote for the day:
"Leadership - leadership is about taking responsibility, not making excuses." -- Mitt Romney
No comments:
Post a Comment