Forrester exec on robotic process automation’s ‘defining point’
 Building a good feedback loop will also be essential. Adding better analytics
and process discovery can train the AIs and allow them to deliver better
recommendations while also shouldering more of the load. “The integration of
process mining, digital work analytics, and machine learning will, in the short
term, help generate RPA scripts that mimic the capabilities of humans, and, in
the long term, help design more-advanced human-machine or human-in-the-loop
(HITL) interaction,” the report stated. Another challenge will be finding the
best way to deliver and price the software. Cloud-based services are now common
and customers have the choice between installing the software locally or relying
upon cloud services managed by the vendor. Many vendors often price their
software by the number of so-called “bots” assigned to particular tasks. The
report imagines that more fine-grained precision will offer customers the
ability to move to “consumption-based pricing” that better follows their usage.
“This may be per minute or hour of robot time or per task executed, but it
solves the problem of bot underutilization,” the report predicted.
Building a good feedback loop will also be essential. Adding better analytics
and process discovery can train the AIs and allow them to deliver better
recommendations while also shouldering more of the load. “The integration of
process mining, digital work analytics, and machine learning will, in the short
term, help generate RPA scripts that mimic the capabilities of humans, and, in
the long term, help design more-advanced human-machine or human-in-the-loop
(HITL) interaction,” the report stated. Another challenge will be finding the
best way to deliver and price the software. Cloud-based services are now common
and customers have the choice between installing the software locally or relying
upon cloud services managed by the vendor. Many vendors often price their
software by the number of so-called “bots” assigned to particular tasks. The
report imagines that more fine-grained precision will offer customers the
ability to move to “consumption-based pricing” that better follows their usage.
“This may be per minute or hour of robot time or per task executed, but it
solves the problem of bot underutilization,” the report predicted.Kubernetes hardening: Drilling down on the NSA/CISA guidance
 Your security efforts shouldn’t stop at the pods. Networking within the cluster
is also key to ensuring that malicious activities can’t occur, and if they do,
they can be isolated to mitigate their impact. In addition to securing the
control plane, key recommendations include using network policies and firewalls
to both separate and isolate resources and encrypting traffic in motion and
protecting sensitive data such as secrets at rest. One core way of doing this is
taking advantage of the Kubernetes namespace native functionality. While three
namespaces are built-in by default, you can create additional namespaces for
your applications. Not only does the namespace construct provide isolation, but
it can help use resource policies to limit storage and compute resources at the
namespace level as well. This can prevent resource exhaustion, either by
accident or maliciously, which can have cascading effect on the entire cluster
and all its supported applications. While namespaces can help provide resource
isolation, leveraging network policies can control the flow of traffic between
the various components including pods, namespaces and external IP addresses.
Your security efforts shouldn’t stop at the pods. Networking within the cluster
is also key to ensuring that malicious activities can’t occur, and if they do,
they can be isolated to mitigate their impact. In addition to securing the
control plane, key recommendations include using network policies and firewalls
to both separate and isolate resources and encrypting traffic in motion and
protecting sensitive data such as secrets at rest. One core way of doing this is
taking advantage of the Kubernetes namespace native functionality. While three
namespaces are built-in by default, you can create additional namespaces for
your applications. Not only does the namespace construct provide isolation, but
it can help use resource policies to limit storage and compute resources at the
namespace level as well. This can prevent resource exhaustion, either by
accident or maliciously, which can have cascading effect on the entire cluster
and all its supported applications. While namespaces can help provide resource
isolation, leveraging network policies can control the flow of traffic between
the various components including pods, namespaces and external IP addresses.Conductor: Why We Migrated from Kubernetes to Nomad
 The first major issue we ran into related to this job type was the GKE
autoscaler. As customers’ workload increased, we started to have incidents where
pending jobs were piling up exponentially, but nothing was scaled up. After
examining the Kubernetes source code, we realized that the default Kubernetes
autoscaler is not designed for batch jobs, which typically have a low tolerance
for delay. We also had no control over when the autoscaler started removing
instances. It was set to 10 minutes as a static configuration, but the
accumulated idle time increased our infrastructure cost as we could not rapidly
scale down once there was nothing left to work on. We also discovered that
the Kubernetes job controller, a supervisor for pods carrying out batch
processes, was unreliable. The system would lose track of jobs and be in the
wrong state. And there was another scalability issue. On the control plane side,
there was no visibility into the size of the GKE clusters’ control plane.
As load increases, GKE would automatically scale up the control plane instances
to handle more requests.
The first major issue we ran into related to this job type was the GKE
autoscaler. As customers’ workload increased, we started to have incidents where
pending jobs were piling up exponentially, but nothing was scaled up. After
examining the Kubernetes source code, we realized that the default Kubernetes
autoscaler is not designed for batch jobs, which typically have a low tolerance
for delay. We also had no control over when the autoscaler started removing
instances. It was set to 10 minutes as a static configuration, but the
accumulated idle time increased our infrastructure cost as we could not rapidly
scale down once there was nothing left to work on. We also discovered that
the Kubernetes job controller, a supervisor for pods carrying out batch
processes, was unreliable. The system would lose track of jobs and be in the
wrong state. And there was another scalability issue. On the control plane side,
there was no visibility into the size of the GKE clusters’ control plane.
As load increases, GKE would automatically scale up the control plane instances
to handle more requests. Attackers Actively Exploiting Realtek SDK Flaws
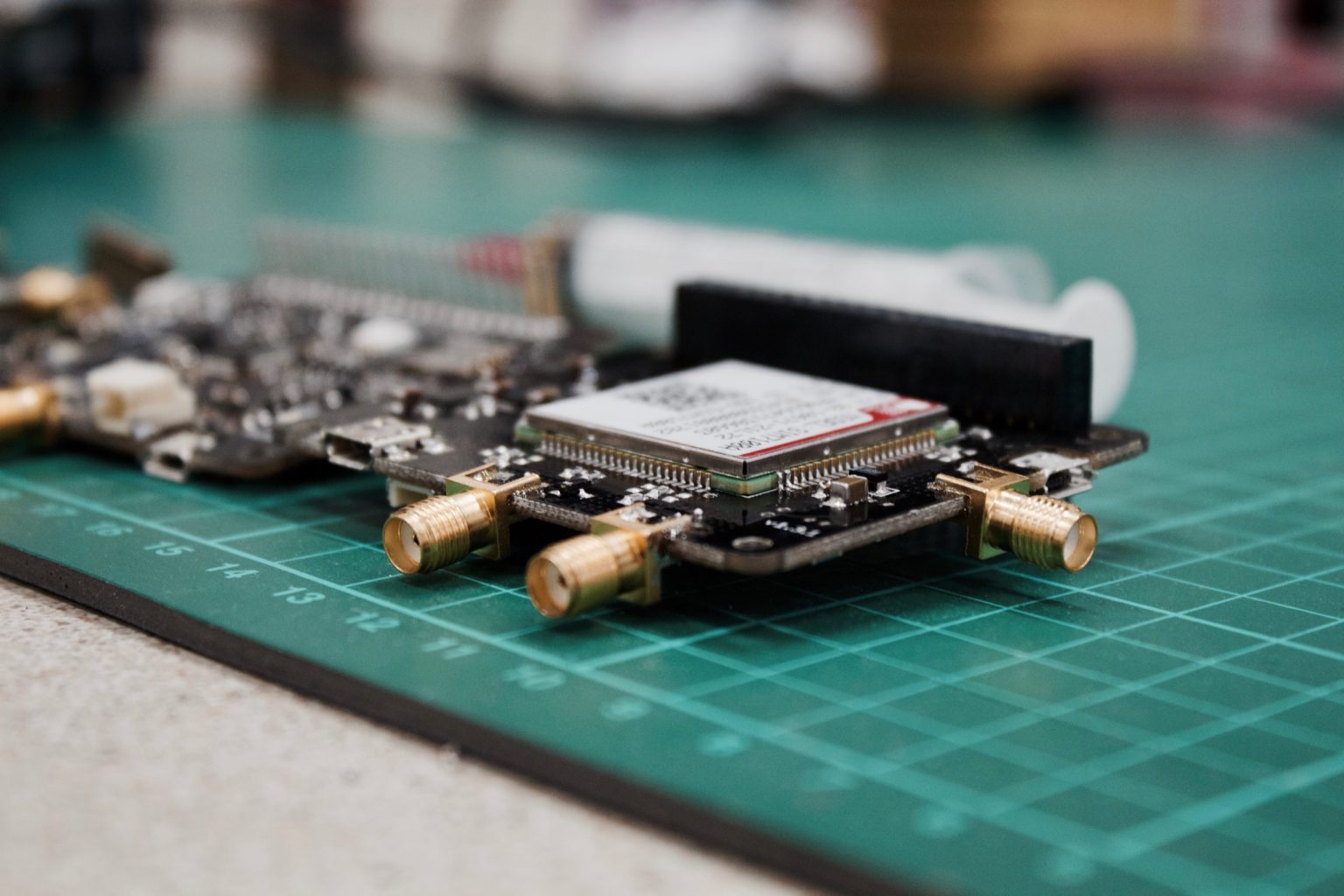
 “Specifically, we noticed exploit attempts to ‘formWsc’ and ‘formSysCmd’ web
pages,” SAM’s report on the incident said. “The exploit attempts to deploy a
Mirai variant detected in March by Palo Alto Networks. Mirai is a notorious IoT
and router malware circulating in various forms for the last 5 years. It was
originally used to shut down large swaths of the internet but has since evolved
into many variants for different purposes.” The report goes on to link another
similar attack to the attack group. On Aug. 6 Juniper Networks found a
vulnerability that just two days later was also exploited to try and deliver the
same Mirai botnet using the same network subnet, the report explained. “This
chain of events shows that hackers are actively looking for command injection
vulnerabilities and use them to propagate widely used malware quickly,” SAM
said. “These kinds of vulnerabilities are easy to exploit and can be integrated
quickly into existing hacking frameworks that attackers employ, well before
devices are patched and security vendors can react.”
“Specifically, we noticed exploit attempts to ‘formWsc’ and ‘formSysCmd’ web
pages,” SAM’s report on the incident said. “The exploit attempts to deploy a
Mirai variant detected in March by Palo Alto Networks. Mirai is a notorious IoT
and router malware circulating in various forms for the last 5 years. It was
originally used to shut down large swaths of the internet but has since evolved
into many variants for different purposes.” The report goes on to link another
similar attack to the attack group. On Aug. 6 Juniper Networks found a
vulnerability that just two days later was also exploited to try and deliver the
same Mirai botnet using the same network subnet, the report explained. “This
chain of events shows that hackers are actively looking for command injection
vulnerabilities and use them to propagate widely used malware quickly,” SAM
said. “These kinds of vulnerabilities are easy to exploit and can be integrated
quickly into existing hacking frameworks that attackers employ, well before
devices are patched and security vendors can react.”The difference between digitization, digitalization & digital transformation
 Digitization is the process of changing from an analog to digital form, also
known as digital enablement. In other words, digitization takes an analog
process and changes it to a digital form without any different-in-kind changes
to the process itself. ... Now, perhaps more disputed is the definition of
digitalization. According to Gartner, we can define it as the use of digital
technologies to change a business model and provide new revenue and
value-producing opportunities. This means that businesses can start to use their
digitized data. Through advanced technologies, businesses will be able to
discover the potential of processed digital data and help them achieve their
business goals. ... Finally, we are introduced to the concept of digital
transformation. Here, Gartner states that digital transformation can refer to
anything from IT modernization, for example, Cloud computing, to digital
optimization, to the invention of new digital business models. Namely, this is
the process of fully benefiting from the enormous digital potential in a
business.
Digitization is the process of changing from an analog to digital form, also
known as digital enablement. In other words, digitization takes an analog
process and changes it to a digital form without any different-in-kind changes
to the process itself. ... Now, perhaps more disputed is the definition of
digitalization. According to Gartner, we can define it as the use of digital
technologies to change a business model and provide new revenue and
value-producing opportunities. This means that businesses can start to use their
digitized data. Through advanced technologies, businesses will be able to
discover the potential of processed digital data and help them achieve their
business goals. ... Finally, we are introduced to the concept of digital
transformation. Here, Gartner states that digital transformation can refer to
anything from IT modernization, for example, Cloud computing, to digital
optimization, to the invention of new digital business models. Namely, this is
the process of fully benefiting from the enormous digital potential in a
business. Bootstrapping the Authentication Layer and Server With Auth0.js and Hasura
Hasura is a GraphQL engine for PostgreSQL databases. Hasura is also not the only available GraphQL engine. There are other solutions like Postgraphile and Prisma. However, after trying a few of them, I've come to appreciate Hasura for several reasons: Hasura is designed for client-facing applications and is one of the simplest solutions to set up. With Hasura, you get a production-level GraphQL server out-of-the-box that’s performant and has a built-in caching system; Powerful authentication engine that’s based on the RLS (Row Level Security) that allows building granular and complex permission systems; You can host Hasura on-premise using their Docker image, but you can also set up a working GraphQL server in a matter of minutes using Hasura cloud. This option is perfect for scaffolding your app and is the one we will use today; Hasura's dashboard is powerful and user-friendly. You can write and test your GraphQL queries, manage your database schema, add custom resolvers and create subscriptions, all from one place.Why Work-From-Home IT Teams May Be at a Greater Risk for Burnout
 Typical burnout indicators include a loss of interest, reduced productivity,
and an inability to fully discharge their professional duties. “People may
also experience high levels of exhaustion, stress, anxiety, and pessimism,”
notes Joe Flanagan, senior employment advisor at online employment services
provider VelvetJobs. Flanagan stated that burnout can also lead to, or
trigger, other mental health issues. “Employers and managers should be trained
and sensitized to identify these signs, and teams must have checks and
balances to provide support to individuals who are at a higher risk,” he
advises. Immediate action is necessary as soon as burnout is suspected in a
team or a specific worker, Welch suggests. The solution may be as simple as
extending a deadline or offering additional support. He also advises
establishing communication channels, such as team video calls, which will
allow colleagues to interact with each other, exchanging news, insights, and
other types of chitchat. “Every team is different, so look for whatever works
for the team,” Welch says.
Typical burnout indicators include a loss of interest, reduced productivity,
and an inability to fully discharge their professional duties. “People may
also experience high levels of exhaustion, stress, anxiety, and pessimism,”
notes Joe Flanagan, senior employment advisor at online employment services
provider VelvetJobs. Flanagan stated that burnout can also lead to, or
trigger, other mental health issues. “Employers and managers should be trained
and sensitized to identify these signs, and teams must have checks and
balances to provide support to individuals who are at a higher risk,” he
advises. Immediate action is necessary as soon as burnout is suspected in a
team or a specific worker, Welch suggests. The solution may be as simple as
extending a deadline or offering additional support. He also advises
establishing communication channels, such as team video calls, which will
allow colleagues to interact with each other, exchanging news, insights, and
other types of chitchat. “Every team is different, so look for whatever works
for the team,” Welch says.Post-Brexit: how has data protection compliance changed?
 While much of The European Union’s General Data Protection Regulations (GDPR)
have been incorporated into UK law, it’s still important to consider what has
changed in terms of how companies – particularly UK-based ones – ensure
compliance to data protection regulations. It was argued in 2017 by Index
Engines that GDPR puts personal data back in the hands of citizens. This
raises the question: “Does this still apply?” No matter what has changed, one
challenge will remain: organisations’ ability to find business and
legal-critical information within their vast unstructured data stores. Then
there are the decisions about when to delete and where to store it, when to
modify and rectify it. This is a complex issue now involving multiple
petabytes of data, and organisations have no real understanding of what their
unstructured data contains. With this top of mind, there is arguably a need
for Wide Area Network (WAN) acceleration to gain the ability to find and move
data around at high speed by mitigating latency and packet loss. This works to
provide quicker data access and retrieval.
While much of The European Union’s General Data Protection Regulations (GDPR)
have been incorporated into UK law, it’s still important to consider what has
changed in terms of how companies – particularly UK-based ones – ensure
compliance to data protection regulations. It was argued in 2017 by Index
Engines that GDPR puts personal data back in the hands of citizens. This
raises the question: “Does this still apply?” No matter what has changed, one
challenge will remain: organisations’ ability to find business and
legal-critical information within their vast unstructured data stores. Then
there are the decisions about when to delete and where to store it, when to
modify and rectify it. This is a complex issue now involving multiple
petabytes of data, and organisations have no real understanding of what their
unstructured data contains. With this top of mind, there is arguably a need
for Wide Area Network (WAN) acceleration to gain the ability to find and move
data around at high speed by mitigating latency and packet loss. This works to
provide quicker data access and retrieval.What the US Army can teach us about building resilient teams
 Science and stories are two of the best ways to defeat skepticism. Gen. Casey
approached Dr. Seligman and his team at the University of Pennsylvania because
it was one of the few known institutions that had conducted large-scale
training on resilience and had published extensive peer-reviewed research in
the area. It was also the only known entity that had extensive experience
developing and implementing a resilience train-the-trainer model that had also
been scientifically reviewed. ... Holistic programs have the power to inspire
and transform an entire organization and those who work in it, and stories of
transformation make the work come to life and help concepts stick. The last
place I thought I would learn anything about vulnerability was with US Army
drill sergeants. Yet I can speak personally about my own transformation
working with them. I used to be someone who never talked about failure or my
own challenges. It was too risky, especially when I was practicing law. But
the soldiers helped me understand that talking about your obstacles isn’t a
sign of weakness—it’s courageous and inspiring. Here are two examples.
Science and stories are two of the best ways to defeat skepticism. Gen. Casey
approached Dr. Seligman and his team at the University of Pennsylvania because
it was one of the few known institutions that had conducted large-scale
training on resilience and had published extensive peer-reviewed research in
the area. It was also the only known entity that had extensive experience
developing and implementing a resilience train-the-trainer model that had also
been scientifically reviewed. ... Holistic programs have the power to inspire
and transform an entire organization and those who work in it, and stories of
transformation make the work come to life and help concepts stick. The last
place I thought I would learn anything about vulnerability was with US Army
drill sergeants. Yet I can speak personally about my own transformation
working with them. I used to be someone who never talked about failure or my
own challenges. It was too risky, especially when I was practicing law. But
the soldiers helped me understand that talking about your obstacles isn’t a
sign of weakness—it’s courageous and inspiring. Here are two examples.How do you lead hybrid teams? 5 essentials
 Transparency is often a leadership virtue in any type of organization, but
it’s an absolute must for hybrid teams. It’s the basis for mutual trust and
productivity when people aren’t consistently working together in the same
location. This starts with a clear, highly visible method of setting goals and
expectations – and a shared belief in how you’re tracking progress. “Leaders
need to be transparent on a shared set of objectives and how they are
measuring employee productivity,” says Thomas Phelps, CIO at Laserfiche. “For
me, it’s not about how many hours you work or when you were last online.” ...
Making broad assumptions about everyone’s shared understanding and experience
is probably a bad idea in a hybrid work mode, for example. Make sure you’re
checking in with people, listening to them, and making positive changes when
they’re in order. Phelps says Laserfiche has been regularly soliciting
employee feedback about current and future operational plans since the
company’s pivot to fully remote/WFH last year. Nayan Naidu, head of DevOps and
cloud engineering capability center at Altimetrik, likewise emphasizes the
importance of transparently setting expectations and reinforcing them
regularly.
Transparency is often a leadership virtue in any type of organization, but
it’s an absolute must for hybrid teams. It’s the basis for mutual trust and
productivity when people aren’t consistently working together in the same
location. This starts with a clear, highly visible method of setting goals and
expectations – and a shared belief in how you’re tracking progress. “Leaders
need to be transparent on a shared set of objectives and how they are
measuring employee productivity,” says Thomas Phelps, CIO at Laserfiche. “For
me, it’s not about how many hours you work or when you were last online.” ...
Making broad assumptions about everyone’s shared understanding and experience
is probably a bad idea in a hybrid work mode, for example. Make sure you’re
checking in with people, listening to them, and making positive changes when
they’re in order. Phelps says Laserfiche has been regularly soliciting
employee feedback about current and future operational plans since the
company’s pivot to fully remote/WFH last year. Nayan Naidu, head of DevOps and
cloud engineering capability center at Altimetrik, likewise emphasizes the
importance of transparently setting expectations and reinforcing them
regularly. Quote for the day:
"It is, after all, the responsibility of the expert to operate the familiar and that of the leader to transcend it." -- Henry A. Kissinger