Quote for the day:
"Management is about arranging and telling. Leadership is about nurturing and enhancing." -- Tom Peters
🎧 Listen to this digest on YouTube Music
▶ Play Audio DigestDuration: 22 mins • Perfect for listening on the go.
Three ways AI is learning to understand the physical world
 The VentureBeat article "Three ways AI is learning to understand the physical
world" explores how researchers are overcoming the physical reasoning
limitations of large language models through "world models." While LLMs excel at
abstract knowledge, they lack grounding in causality, prompting a shift toward
three distinct architectural approaches to simulate the real world. The first,
Joint Embedding Predictive Architecture (JEPA), mimics human cognition by
learning abstract latent features, ignoring irrelevant pixels to achieve the
high efficiency required for real-time robotics. The second approach utilizes
Gaussian splats to generate detailed 3D spatial environments from prompts,
allowing AI agents to interact within standard physics engines like Unreal
Engine. Finally, end-to-end generative models, such as DeepMind’s Genie 3 and
Nvidia’s Cosmos, act as native physics engines by continuously generating frames
and physical dynamics on the fly. This third method is particularly vital for
creating massive synthetic data factories to safely train autonomous systems in
complex edge cases. Ultimately, the analysis suggests a future defined by hybrid
architectures, where LLMs provide the reasoning interface while world models
serve as the foundational infrastructure for spatial data, enabling AI to move
beyond digital browsers and into physical spaces.
The VentureBeat article "Three ways AI is learning to understand the physical
world" explores how researchers are overcoming the physical reasoning
limitations of large language models through "world models." While LLMs excel at
abstract knowledge, they lack grounding in causality, prompting a shift toward
three distinct architectural approaches to simulate the real world. The first,
Joint Embedding Predictive Architecture (JEPA), mimics human cognition by
learning abstract latent features, ignoring irrelevant pixels to achieve the
high efficiency required for real-time robotics. The second approach utilizes
Gaussian splats to generate detailed 3D spatial environments from prompts,
allowing AI agents to interact within standard physics engines like Unreal
Engine. Finally, end-to-end generative models, such as DeepMind’s Genie 3 and
Nvidia’s Cosmos, act as native physics engines by continuously generating frames
and physical dynamics on the fly. This third method is particularly vital for
creating massive synthetic data factories to safely train autonomous systems in
complex edge cases. Ultimately, the analysis suggests a future defined by hybrid
architectures, where LLMs provide the reasoning interface while world models
serve as the foundational infrastructure for spatial data, enabling AI to move
beyond digital browsers and into physical spaces.Field workers don’t need more access, they need better security
In this interview, Chris Thompson, CISO at West Shore Home, outlines the evolving landscape of cybersecurity for field-based workforces. He emphasizes that the principle of least privilege should be applied consistently across all roles, dismissing the notion that field workers require broader access for convenience. A significant shift involves replacing antiquated, shared generic accounts with individual credentials secured by robust multifactor authentication, reflecting a modern standard where security is never sacrificed for speed. Thompson details how West Shore Home manages sensitive customer data through continuous risk assessments and bi-monthly executive reviews, ensuring mitigation strategies remain agile rather than stuck in traditional annual cycles. Addressing the logistical hurdles of training, he advocates for integrating security awareness into daily "toolbox talks" at warehouses, which proves more effective than email-based modules for employees on the move. By aligning security protocols with the technology field teams use daily, the organization fosters a unified culture where every worker understands their role in the broader security posture. Ultimately, Thompson argues that field workers do not need expanded access; they require more sophisticated, integrated security measures that support their unique operational environment without introducing unnecessary risk to the enterprise.6 innovation curves are rewriting enterprise IT strategy
 The article "6 innovation curves are rewriting enterprise IT strategy"
highlights a fundamental shift from sequential technology updates to managing
multiple, overlapping waves of digital transformation. These six innovation
curves include transitioning from traditional software to systems of autonomous
collaborators, adopting AI-native applications that embed machine learning into
their core architecture, and treating enterprise memory as a queryable knowledge
layer for real-time decision-making. Additionally, IT leaders must redesign
human-machine interactions to enhance productivity, establish robust governance
for trust and integrity in a world of synthetic data, and utilize virtual
simulations to de-risk experimentation. The author emphasizes that these curves
are deeply interdependent; for example, autonomous agents require high-quality
memory layers to function effectively, while simulation environments provide the
necessary testing grounds for AI-native interactions. To succeed, organizations
must move beyond linear management models and instead develop an integrated
strategy that orchestrates these curves concurrently. By focusing on areas like
"AgentOps" and persistent data layers, businesses can build a resilient digital
architecture capable of absorbing continuous disruption while maintaining
operational priorities, effectively redefining how enterprises create value and
manage risk in an AI-driven landscape.
The article "6 innovation curves are rewriting enterprise IT strategy"
highlights a fundamental shift from sequential technology updates to managing
multiple, overlapping waves of digital transformation. These six innovation
curves include transitioning from traditional software to systems of autonomous
collaborators, adopting AI-native applications that embed machine learning into
their core architecture, and treating enterprise memory as a queryable knowledge
layer for real-time decision-making. Additionally, IT leaders must redesign
human-machine interactions to enhance productivity, establish robust governance
for trust and integrity in a world of synthetic data, and utilize virtual
simulations to de-risk experimentation. The author emphasizes that these curves
are deeply interdependent; for example, autonomous agents require high-quality
memory layers to function effectively, while simulation environments provide the
necessary testing grounds for AI-native interactions. To succeed, organizations
must move beyond linear management models and instead develop an integrated
strategy that orchestrates these curves concurrently. By focusing on areas like
"AgentOps" and persistent data layers, businesses can build a resilient digital
architecture capable of absorbing continuous disruption while maintaining
operational priorities, effectively redefining how enterprises create value and
manage risk in an AI-driven landscape.Credential theft compounded in 2025, says new data from Recorded Future
 Recorded Future’s 2025 Identity Threat Landscape Report reveals that credential
theft has become the primary initial access vector for enterprise security
breaches, characterized by a staggering escalation throughout the year. Data
indicates that credential indexing surged by 90 percent in the final quarter
compared to the first, with a significant majority of these attacks specifically
targeting authentication systems to maximize unauthorized access. A particularly
alarming trend is the proliferation of infostealer malware, which harvested 276
million credentials containing active session cookies. These cookies enable
cybercriminals to bypass multi-factor authentication entirely, rendering
traditional security measures increasingly insufficient. The report underscores
that a single compromised endpoint can jeopardize an entire organization, as the
average infected device now yields approximately 87 distinct stolen credentials
across various corporate and personal platforms. Consequently, industry experts
advocate for a transition toward "verified trust" models, which emphasize
continuous, contextual identity verification using biometrics and passkeys.
Despite the escalating risk, research from IDC and Ping Identity suggests that
only nine percent of organizations have successfully operationalized these
advanced safeguards at scale, highlighting a critical maturity gap in global
digital infrastructure and a pressing need for board-level prioritization of
identity security.
Recorded Future’s 2025 Identity Threat Landscape Report reveals that credential
theft has become the primary initial access vector for enterprise security
breaches, characterized by a staggering escalation throughout the year. Data
indicates that credential indexing surged by 90 percent in the final quarter
compared to the first, with a significant majority of these attacks specifically
targeting authentication systems to maximize unauthorized access. A particularly
alarming trend is the proliferation of infostealer malware, which harvested 276
million credentials containing active session cookies. These cookies enable
cybercriminals to bypass multi-factor authentication entirely, rendering
traditional security measures increasingly insufficient. The report underscores
that a single compromised endpoint can jeopardize an entire organization, as the
average infected device now yields approximately 87 distinct stolen credentials
across various corporate and personal platforms. Consequently, industry experts
advocate for a transition toward "verified trust" models, which emphasize
continuous, contextual identity verification using biometrics and passkeys.
Despite the escalating risk, research from IDC and Ping Identity suggests that
only nine percent of organizations have successfully operationalized these
advanced safeguards at scale, highlighting a critical maturity gap in global
digital infrastructure and a pressing need for board-level prioritization of
identity security.Configuration as a Control Plane: Designing for Safety and Reliability at Scale
/articles/configuration-control-plane/en/smallimage/configuration-as-a-control-plane-designing-for-safety-and-reliability-at-scale-thumb-1773657574566.jpg) The InfoQ article "Configuration as a Control Plane" explores the evolution of
configuration from static deployment files into a dynamic, live control plane
that actively shapes system behavior. In modern cloud-native architectures,
configuration changes often move faster and impact more systems than application
code, making them a primary driver of large-scale reliability incidents.
Consequently, configuration management is transitioning from traditional
agent-based convergence toward continuously reconciled, policy-enforced systems.
The article emphasizes treating configuration as a high-leverage reliability
discipline rather than a mere operational task. Key strategies discussed include
using strongly typed, schema-validated configurations and policy engines like
Open Policy Agent (OPA) to enforce guardrails before and during rollouts. By
adopting practices such as staged regional rollouts, canary deployments, and
automated diff analysis, organizations can ensure that configuration correctness
is a systemic property rather than a manual checklist. Looking ahead, the
integration of AI-driven risk assessment and unified configuration APIs promises
to further enhance safety and resilience. Ultimately, this shift enables
infrastructure to become more self-healing and predictable, allowing teams to
manage complex, ephemeral workloads at scale while minimizing the risk of
catastrophic human error or cascading failures.
The InfoQ article "Configuration as a Control Plane" explores the evolution of
configuration from static deployment files into a dynamic, live control plane
that actively shapes system behavior. In modern cloud-native architectures,
configuration changes often move faster and impact more systems than application
code, making them a primary driver of large-scale reliability incidents.
Consequently, configuration management is transitioning from traditional
agent-based convergence toward continuously reconciled, policy-enforced systems.
The article emphasizes treating configuration as a high-leverage reliability
discipline rather than a mere operational task. Key strategies discussed include
using strongly typed, schema-validated configurations and policy engines like
Open Policy Agent (OPA) to enforce guardrails before and during rollouts. By
adopting practices such as staged regional rollouts, canary deployments, and
automated diff analysis, organizations can ensure that configuration correctness
is a systemic property rather than a manual checklist. Looking ahead, the
integration of AI-driven risk assessment and unified configuration APIs promises
to further enhance safety and resilience. Ultimately, this shift enables
infrastructure to become more self-healing and predictable, allowing teams to
manage complex, ephemeral workloads at scale while minimizing the risk of
catastrophic human error or cascading failures.
10 Million IoT Devices Hacked: Is Yours Next?
 The Medium article "10 Million IoT Devices Hacked: Is Yours Next?" explores the
alarming rise of BadBox 2.0, a sophisticated global botnet that has compromised
over ten million Internet of Things (IoT) devices. Highlighting a 2025 federal
lawsuit by Google, the piece details how seemingly harmless gadgets—such as
unbranded streaming boxes, digital picture frames, and car infotainment
systems—are being transformed into criminal infrastructure. A critical
revelation is that many of these devices are pre-infected with malware during
manufacturing, meaning consumers are compromised the moment they connect to
Wi-Fi. The vulnerability primarily affects cheap hardware running the Android
Open Source Project (AOSP) without Google’s Play Protect certification. To
safeguard home networks, the author recommends identifying all connected devices
via router admin panels and scanning for red flags like "Seekiny Studio" apps or
unusual traffic to foreign IP ranges. Ultimately, the article serves as a stark
warning against purchasing low-cost, unverified electronics, urging users to
prioritize "purchase hygiene" by sticking to reputable brands with verifiable
firmware update histories. By verifying Play Protect status and monitoring for
network anomalies, users can better defend their digital privacy against these
pervasive, invisible threats.
The Medium article "10 Million IoT Devices Hacked: Is Yours Next?" explores the
alarming rise of BadBox 2.0, a sophisticated global botnet that has compromised
over ten million Internet of Things (IoT) devices. Highlighting a 2025 federal
lawsuit by Google, the piece details how seemingly harmless gadgets—such as
unbranded streaming boxes, digital picture frames, and car infotainment
systems—are being transformed into criminal infrastructure. A critical
revelation is that many of these devices are pre-infected with malware during
manufacturing, meaning consumers are compromised the moment they connect to
Wi-Fi. The vulnerability primarily affects cheap hardware running the Android
Open Source Project (AOSP) without Google’s Play Protect certification. To
safeguard home networks, the author recommends identifying all connected devices
via router admin panels and scanning for red flags like "Seekiny Studio" apps or
unusual traffic to foreign IP ranges. Ultimately, the article serves as a stark
warning against purchasing low-cost, unverified electronics, urging users to
prioritize "purchase hygiene" by sticking to reputable brands with verifiable
firmware update histories. By verifying Play Protect status and monitoring for
network anomalies, users can better defend their digital privacy against these
pervasive, invisible threats.
How CISOs Can Survive the Era of Geopolitical Cyberattacks
 In the current era of geopolitical cyber warfare, Chief Information Security
Officers (CISOs) must pivot from traditional perimeter defense to a robust
strategy of internal containment. Geopolitical attacks, exemplified by Iranian
wiper campaigns like the Handala group’s strike on Stryker, differ from standard
ransomware because they prioritize operational chaos and destruction over
financial gain. To survive these threats, the article outlines a vital five-step
playbook centered on limiting lateral movement. First, CISOs should implement
identity-aware access controls to prevent compromised credentials from granting
broad network access. Second, they must enforce default-deny policies on
administrative ports to block common pivot points. Third, restricting privileged
accounts through role-based segmentation is essential to reduce the potential
blast radius of a breach. Fourth, organizations need deep visibility into
internal traffic to detect covert tunnels and unauthorized connection paths.
Finally, implementing automated isolation capabilities ensures that destructive
activity is contained before it can spread across the entire infrastructure.
Ultimately, the transition to a self-defending network that focuses on stopping
an attacker’s mobility rather than just their entry is crucial. By treating
internal connectivity as a primary risk factor, CISOs can ensure their
organizations remain operational despite increasingly sophisticated,
state-sponsored cyber disruptions.
In the current era of geopolitical cyber warfare, Chief Information Security
Officers (CISOs) must pivot from traditional perimeter defense to a robust
strategy of internal containment. Geopolitical attacks, exemplified by Iranian
wiper campaigns like the Handala group’s strike on Stryker, differ from standard
ransomware because they prioritize operational chaos and destruction over
financial gain. To survive these threats, the article outlines a vital five-step
playbook centered on limiting lateral movement. First, CISOs should implement
identity-aware access controls to prevent compromised credentials from granting
broad network access. Second, they must enforce default-deny policies on
administrative ports to block common pivot points. Third, restricting privileged
accounts through role-based segmentation is essential to reduce the potential
blast radius of a breach. Fourth, organizations need deep visibility into
internal traffic to detect covert tunnels and unauthorized connection paths.
Finally, implementing automated isolation capabilities ensures that destructive
activity is contained before it can spread across the entire infrastructure.
Ultimately, the transition to a self-defending network that focuses on stopping
an attacker’s mobility rather than just their entry is crucial. By treating
internal connectivity as a primary risk factor, CISOs can ensure their
organizations remain operational despite increasingly sophisticated,
state-sponsored cyber disruptions.
Building A Sustainable Hustle Culture
 In "Building A Sustainable Hustle Culture," Greg Dolan, CEO of Keen Decision
Systems, critiques the traditional "work hard, play hard" model for its tendency
to cause burnout and employee dissatisfaction. Instead, he advocates for a
reimagined "smart hustle" that prioritizes work-life integration and mental
well-being over relentless overwork. Central to this approach is the
implementation of a four-day workweek, which Dolan argues allows for the deep
rest necessary for high performance. By establishing clear temporal constraints,
employees are encouraged to maximize their focus during work hours while fully
disconnecting during their time off. This period of rest often serves as a
catalyst for innovation, as personal interactions and downtime can unlock fresh
professional insights. Despite the fact that only 22% of American employers have
adopted this schedule, Dolan highlights research showing that 98% of employees
feel significantly more motivated under such a model. Ultimately, the article
suggests that sustainable success is achieved not through endless hours, but by
valuing employee autonomy and recognizing that a refreshed workforce is
inherently more productive and creative, transforming the very definition of
professional ambition and organizational health in the modern era.
In "Building A Sustainable Hustle Culture," Greg Dolan, CEO of Keen Decision
Systems, critiques the traditional "work hard, play hard" model for its tendency
to cause burnout and employee dissatisfaction. Instead, he advocates for a
reimagined "smart hustle" that prioritizes work-life integration and mental
well-being over relentless overwork. Central to this approach is the
implementation of a four-day workweek, which Dolan argues allows for the deep
rest necessary for high performance. By establishing clear temporal constraints,
employees are encouraged to maximize their focus during work hours while fully
disconnecting during their time off. This period of rest often serves as a
catalyst for innovation, as personal interactions and downtime can unlock fresh
professional insights. Despite the fact that only 22% of American employers have
adopted this schedule, Dolan highlights research showing that 98% of employees
feel significantly more motivated under such a model. Ultimately, the article
suggests that sustainable success is achieved not through endless hours, but by
valuing employee autonomy and recognizing that a refreshed workforce is
inherently more productive and creative, transforming the very definition of
professional ambition and organizational health in the modern era.
5 Production Scaling Challenges for Agentic AI in 2026
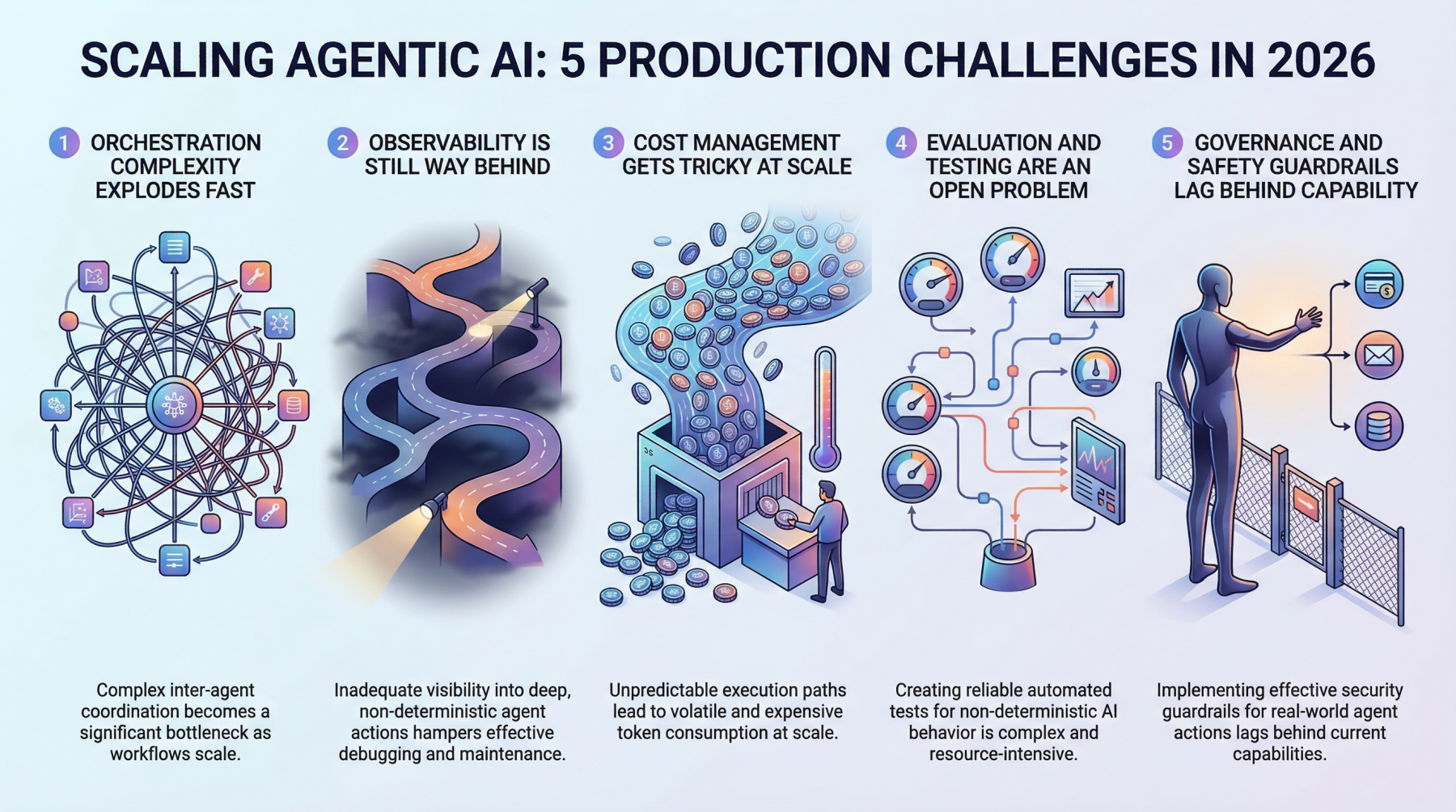 In the article "5 Production Scaling Challenges for Agentic AI in 2026," Nahla
Davies examines the significant hurdles organizations face when moving
autonomous systems from prototype to large-scale production. The first major
obstacle is orchestration complexity, which grows exponentially in multi-agent
environments where coordination overhead often becomes a performance bottleneck.
Second, current observability tools remain inadequate for tracing the
non-deterministic, multi-step decision paths inherent in agentic workflows,
making debugging a profound challenge. Third, cost management is increasingly
difficult as autonomous loops consume tokens rapidly, with variable execution
paths creating high billing unpredictability. Fourth, traditional testing and
evaluation methods are insufficient for probabilistic systems; teams must
instead develop advanced simulation environments or "LLM-as-a-judge" pipelines
to ensure reliability. Finally, the rapid deployment of agentic capabilities has
outpaced governance and safety frameworks. Implementing robust guardrails is
essential to prevent harmful real-world actions—such as unauthorized
transactions or database modifications—without stifling the agent’s practical
utility. Ultimately, the analysis highlights that while agentic AI is
transformative, bridging the production gap requires solving these foundational
infrastructure and safety problems to move beyond "pilot purgatory" into
meaningful, scaled operations.
In the article "5 Production Scaling Challenges for Agentic AI in 2026," Nahla
Davies examines the significant hurdles organizations face when moving
autonomous systems from prototype to large-scale production. The first major
obstacle is orchestration complexity, which grows exponentially in multi-agent
environments where coordination overhead often becomes a performance bottleneck.
Second, current observability tools remain inadequate for tracing the
non-deterministic, multi-step decision paths inherent in agentic workflows,
making debugging a profound challenge. Third, cost management is increasingly
difficult as autonomous loops consume tokens rapidly, with variable execution
paths creating high billing unpredictability. Fourth, traditional testing and
evaluation methods are insufficient for probabilistic systems; teams must
instead develop advanced simulation environments or "LLM-as-a-judge" pipelines
to ensure reliability. Finally, the rapid deployment of agentic capabilities has
outpaced governance and safety frameworks. Implementing robust guardrails is
essential to prevent harmful real-world actions—such as unauthorized
transactions or database modifications—without stifling the agent’s practical
utility. Ultimately, the analysis highlights that while agentic AI is
transformative, bridging the production gap requires solving these foundational
infrastructure and safety problems to move beyond "pilot purgatory" into
meaningful, scaled operations.
Building trust in the future of quantum computing
 The article "The Future of Quantum," published on Phys.org in March 2026,
outlines a pivotal transition in quantum science from experimental
demonstrations to "utility-scale" industrial applications. As the field marks
the centennial of quantum mechanics, researchers are shifting focus from simply
increasing qubit counts to enhancing system reliability through advanced
error-mitigation and standardized benchmarking. A central theme is "building
trust," which involves creating transparent performance metrics that allow
industries to transition from classical to quantum-enhanced workflows in sectors
like drug discovery, sustainable material design, and financial modeling.
Significant breakthroughs highlighted include the development of diamond-based
quantum internet nodes and the emergence of "quantum batteries" that exhibit
faster charging at larger scales. Additionally, the analysis emphasizes the
geopolitical dimension, noting substantial national investments aimed at
securing sovereign quantum capabilities for national security and economic
resilience. Ultimately, the piece argues that the "second quantum revolution" is
now defined by the convergence of hardware stability and sophisticated software
stacks, effectively turning the strange properties of entanglement and
superposition into dependable tools for global digital infrastructure and
solving previously intractable computational challenges.
The article "The Future of Quantum," published on Phys.org in March 2026,
outlines a pivotal transition in quantum science from experimental
demonstrations to "utility-scale" industrial applications. As the field marks
the centennial of quantum mechanics, researchers are shifting focus from simply
increasing qubit counts to enhancing system reliability through advanced
error-mitigation and standardized benchmarking. A central theme is "building
trust," which involves creating transparent performance metrics that allow
industries to transition from classical to quantum-enhanced workflows in sectors
like drug discovery, sustainable material design, and financial modeling.
Significant breakthroughs highlighted include the development of diamond-based
quantum internet nodes and the emergence of "quantum batteries" that exhibit
faster charging at larger scales. Additionally, the analysis emphasizes the
geopolitical dimension, noting substantial national investments aimed at
securing sovereign quantum capabilities for national security and economic
resilience. Ultimately, the piece argues that the "second quantum revolution" is
now defined by the convergence of hardware stability and sophisticated software
stacks, effectively turning the strange properties of entanglement and
superposition into dependable tools for global digital infrastructure and
solving previously intractable computational challenges.
No comments:
Post a Comment