Network observability: What it means to vendors and to you

Network observability represents an evolution of network monitoring. Network
observability solutions should dive deeper into networks, collecting a more
diverse and voluminous set of data to give network teams total end-to-end
visibility into operations. Those solutions should broaden their scope, looking
not just at network performance, but end-user experience, business impacts, and
security. Finally, network observability should focus less on tinkering with how
it presents data, which ultimately forces network engineers to glean insights
themselves and doing too much of the heavy lifting in their heads. Instead,
network observability should emphasize actionable insights derived in a variety
of ways, including AI and machine learning and low-code scripted automation. The
former relies on algorithms to make tools more intelligent. Many vendors are
driving toward actionable insights with AIOps, and our research shows that
NetOps pros see tremendous potential with these algorithms.
Resume makeover: Transforming a career post-mortem into a C-suite future

One trap IT leaders often fall into when seeking a new job is viewing their
resume as a historical document of their career. The reality is that your resume
should paint a clear picture of your career’s future, detailing your past work
experience as a roadmap that leads inevitably to your next leadership gig. But
striking that balance between detailing the past and mapping toward the future
can be challenging, especially while keeping your resume to-the-point. ... As a
general rule, a professional resume should be a concise 1-2 pages when applying
for corporate roles. Recruiters read through thousands of resumes, so they’re
more likely to lose focus or abandon your resume altogether if they can’t get a
sense of your qualifications within the first few minutes. ... Including
executive summaries and a side bar with your education, skills, and credentials
is a great way to remove redundancies from your work experience, allowing you to
focus on specific accomplishments at each role, while consolidating your
evergreen skills, expertise, and knowledge into short and simple lists.
How to attract more women into software development

Regardless of gender, it boils down to competence and confidence, said Archana.
“Building your competence is extremely important, and with that competence comes
confidence. Keep learning, build your competence, be confident about yourself,
and don’t be worried about too many setbacks,” she added. “When you are a
subject matter expert, the agenda is almost invisible at the table because
people are listening to you for your expert opinions, for your knowledge in the
area. And you want respect from that.” While more could be done to encourage
gender diversity, Manjunatha called for women to upskill often. “Keep yourself
updated,” added Manjunatha. “Technology is constantly evolving. What got you
here is not going to get you there tomorrow, so always keep yourself updated.
The growth mindset and that ability to want to keep learning that’s very, very
important if you’re in this space. While upskill, e-learning or retraining can
be achieved without going through a certification course, Kwong noted that
certification is a means to benchmark one’s competency and skillsets.
Australia seeks stiffer penalty for data breaches
Following the update, companies found to have committed the breaches will be
fined AU$50 million, or three times the value of any benefit it obtained through
the misuse of information, or 30% of the company's adjusted turnover in the
relevant period, whichever is greater. The Bill also will afford the Australian
Information Commissioner "greater power" to resolve privacy breaches as well as
strengthen the Notifiable Data Breaches scheme, which will provide the
Commissioner with full knowledge of information that compromised in a breach so
it can assess the risks of harm to affected individuals. In addition, the
Commissioner as and Australian Communications and Media Authority will be better
empowered to share information in the event of a data breach. Dreyfus said:
"When Australians are asked to hand over their personal data they have a right
to expect it will be protected. Unfortunately, significant privacy breaches in
recent weeks have shown existing safeguards are inadequate.
Does Your Database Really Need to Move to the Cloud?

When it comes to global-scale, multicloud and hybrid use cases, it’s important
to consider how you ensure data remains consistent across regions while ensuring
applications are running as quickly as possible, Powers added. Redis Enterprise
offers Active-Active Geo Distribution, to allow local speed read and writes
while ensuring consistent data is replicated across regions, with less than a
millisecond of latency. So, even if the long-term goal is full application
modernization, Powers said, “There are places where you can still use Oracle or
MySQL, and patch us alongside, to fix it in the interim, while you’re making
these transitions.” In these cases, he argued, “The modernization is around
speed, it’s around scale, it’s around total cost of ownership.” So, the question
of how to modernize your database becomes far more nuanced than whether you can
afford the time and money to embark on a complete refactoring and re-platforming
project.
What challenges are hardest to avoid when managing data in the cloud?
Data is moving to the cloud because it is an excellent place to store, manage,
and analyze data. The cloud breaks down information silos that exist in
on-premises computing, making it much easier to share data internally and with
business partners and customers. However, when you put all your data in one
place, you also must implement safeguards that govern the use of the data — most
importantly data access control. This has proven to be a challenge for
technology vendors and for the organizations that are managing their data in the
cloud. The underlying problem is caused by SQL. The industry-standard database
query language is a core element of the Modern Data Stack, which is the
ecosystem of technologies that enable us to manage data in the cloud. But while
SQL is great for business analytics, it cannot support the complex,
graph-oriented relationships required for data governance.
From zero to 10 million lines of Kotlin

Going into this migration, we had two options: We could make it possible to
write new code at Meta using Kotlin but leave most of the existing code in
Java; We could attempt to convert almost all our in-house code into Kotlin.
The advantage of the first option is clear — it’s much less work. But there are
two notable disadvantages to this approach. First, enabling interoperability
between Kotlin and Java code introduces the use of platform types in Kotlin.
Platform types give rise to runtime null pointer dereferences that result in
crashes instead of the static safety offered by pure Kotlin code. In some
complicated cases, Kotlin’s null check elision can let nulls through and create
surprising null pointer exceptions later. This could happen if, for example,
Kotlin code calls a Kotlin interface implemented by a Java interface. Other
issues include Java’s inability to tag type parameters as nullable (until
recently), and Kotlin’s overloading rules taking nullability into account, while
Java’s overloading rules do not.
Using Remote Agile Governance to Create the Culture Organisations Need
Agility is not a best practice, but a mindset for uncovering good and better
practices. This requires an emergent, context specific good practice of
governance. Remote:AF and Esther Derby have spent the last year working to
generate a process for just this approach to governance. More and more,
organisations are realising that if they truly want to change their culture,
they must change their governance. Agility started with the scrum software team,
spread through the IT department in the form of DevOps, and through the rest of
the organisation in Business Agility - but governance has, until now, been a
holdout from this evolution. As long as it remains so, it has the potential to
have an out-sized impact, holding the business back from true agility. ...
Firstly, let’s define what we mean by governance in the context of this article.
Governance is not (just) forums, meetings, and reports. It is all the ways an
organisation makes decisions to enact strategy.
Digital transformation: 4 questions to help drive momentum
Enterprises often get locked in a cycle, fixing various aspects of customer
experience (CX), operational efficiency, business model innovation, etc. For
example, the most commonly cited business driver for digital transformation is
customer experience. But while implementing it – through mobility, front-end
workflows, and chatbots, for instance – organizations realize that operational
efficiency is equally important, if not more so. So they fix the backend, only
to realize that they’re missing the bus on the business model. And the cycle
continues, making it difficult for enterprises to scale beyond CX use cases in
marketing and customer service. ... Addressing technical debt and legacy
technologies is a difficult challenge. A well-defined architectural blueprint
early on can enable a holistic digital transformation in the long term. It can
help identify the best use cases while balancing quick wins with foundational
elements. However, if you are in the middle of your journey, it’s essential to
tackle the problem of technical debt to move forward.
Why Passkeys Are Better Than Passwords
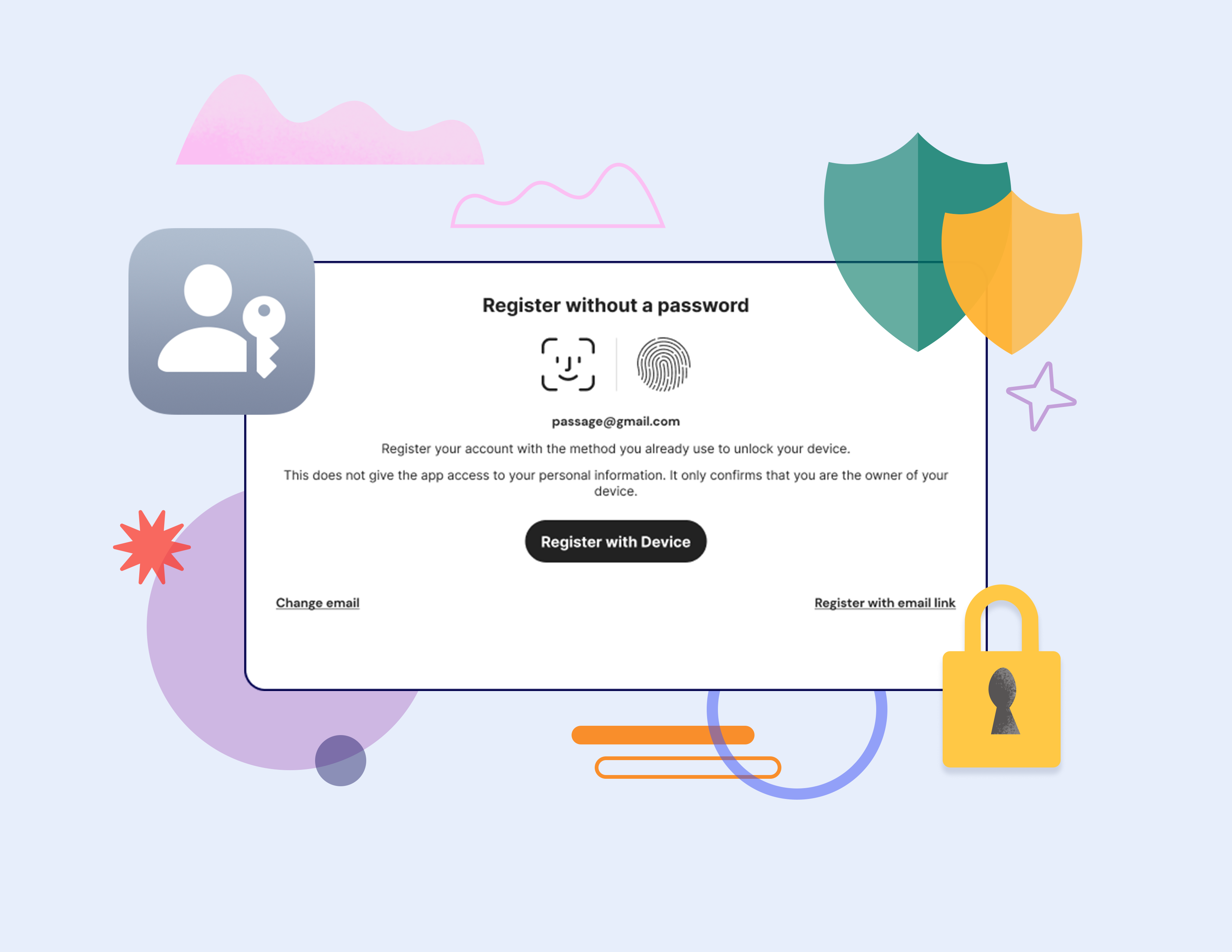
With passkeys, passwords are simply no longer a threat vector. Passwords account
for north of 80% of all security breaches. Passkeys mitigate this threat down to
almost nothing. You can’t reuse your passkeys. You don’t have to remember them.
They are generated and stored for you, so you don’t have to worry about creating
and storing them yourself. You can’t be lured into giving them up because they
are unique to a specific website and thus can’t be shared with a phishing
website. Sensitive data associated with each passkey never leaves your device.
The information is stored on your phone on a special chip (a Trusted Platform
Module) that even the NSA might not be able to crack. If you register with a
website using a passwordless solution like Passage, that site gets nothing but a
public key, which is useless for cracking open your account. While Apple lets
you share your account with others via AirDrop, you couldn’t even share the
actual private key with a phishing site if you wanted to.
Quote for the day:
"One of the sad truths about leadership
is that, the higher up the ladder you travel, the less you know." --
Margaret Heffernan
No comments:
Post a Comment